


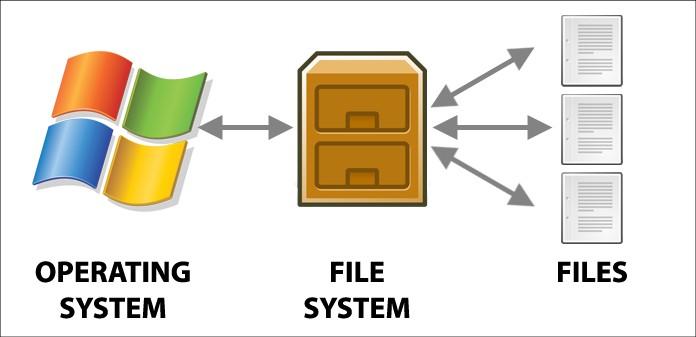
From the user’s point of view, one of the most important parts of an operating system is the file system. The file system provides the resource abstractions typically associated with secondary storage. The file system permits users to create data collections, called files, with desirable properties, such as:
• Long-term existence: Files are stored on disk or other secondary storage and do not disappear when a user logs off.
• Sharable between processes: Files have names and can have associated access permissions that permit controlled sharing.
• Structure: A file can have an internal structure that is convenient for particular applications. In addition, files can be organized into hierarchical or more complex structure to reflect the relationships among files.
File system provides typical operations include the following:
• Create: A new file is defined and positioned within the structure of files.
• Delete: A file is removed from the file structure and destroyed.
• Open: An existing file is declared to be “opened” by a process, allowing the process to perform functions on the file.
• Close: The file is closed with respect to a process, so that the process no longer may perform functions on the file, until the process opens the file again.
• Read: A process reads all or a portion of the data in a file.
• Write: A process updates a file, either by adding new data that expands the size of the file or by changing the values of existing data items in the file.
Typically, a file system maintains a set of attributes associated with the file. These include owner, creation time, time last modified, access privileges, and so on.
File Structure
Four terms are in common use when discussing files:
• Field
• Record
• File
• Database
A field is the basic element of data. An individual field contains a single value, such as an employee’s last name, a date, or the value of a sensor reading. It is characterized by its length and data type (e.g., ASCII string, decimal). Depending on the file design, fields may be fixed length or variable length.
A record is a collection of related fields that can be treated as a unit by some application program. For example, an employee record would contain such fields as name, social security number, job classification, date of hire, and so on. Again, depending on design, records may be of fixed length or variable length. A record will be of variable length if some of its fields are of variable length or if the number of fields may vary.
A file is a collection of similar records. The file is treated as a single entity by users and applications and may be referenced by name. Files have file names and may be created and deleted. Access control restrictions usually apply at the file level.
A database is a collection of related data. The essential aspects of a database are that the relationships that exist among elements of data are explicit and that the database is designed for use by a number of different applications. A database may contain all of the information related to an organization or project, such as a business or a scientific study. The database itself consists of one or more types of files.