


Memory management helps to coordinate n control the computers main memory .
It ensures that the memory space is properly managed and allocated in operating system.
Memory managers enables sharing of memory space between processes. Hence two programs can work at the same memory location although at different times.
There are 3 types of memory management
Hardware memory management.
Operating system memory management.
Application memory management
Example :
If you have a computer of 8 gb of ram and want to run several programs then the memory management helps to ensure that program have enough memory and cab run without interfering with each other
Advantages:
It is a simple management approach
Disadvantages:
It does not support multiprogramming
In memory management the memory unit supports two basic operations: read and write.
The read operation reads previously stored dat
The write operation stores a new value in memory. Both of these operations require a memory address. In addition, the write operation requires specification of the data to be written.
There are several types of computer memory such as random access memory (RAM), read-only memory (ROM), cache memory, virtual memory,
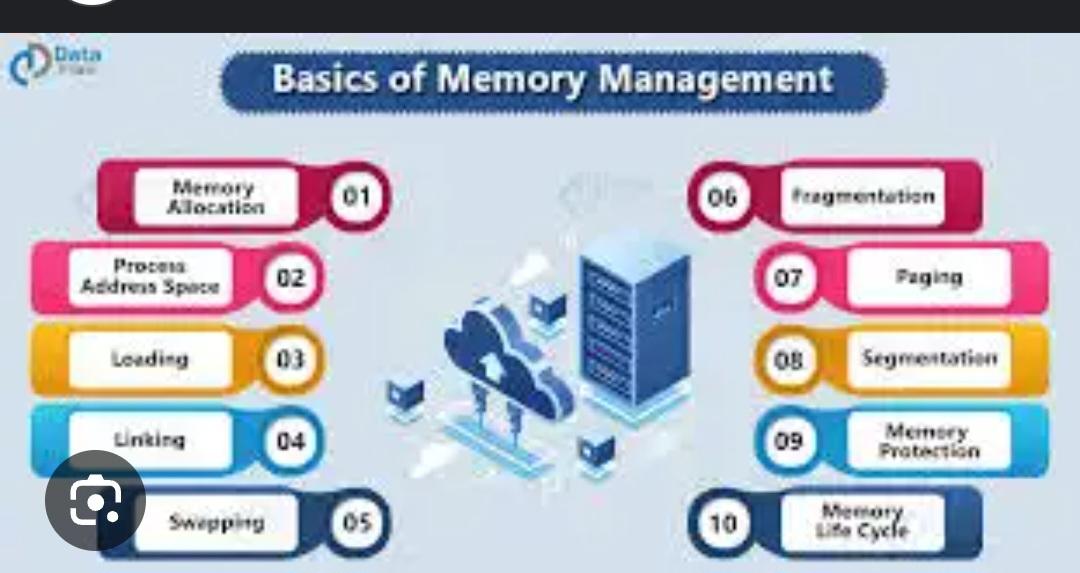
The main activities of memory management are
Thrashing
Memory protection
Page replacement
Swapping
Demand pagging
Virtual memory
Segmentation
Paging
Memory allocation
Etcc
Memoryy allocation has two typess
They aree as follows:
Fixed Partitioning: Memory is divided into fixed-size partitions.
Dynamic Partitioning: Memory is allocated to processes based on their needs
Page relapcement has following types:
FIFO (First-In-First-Out): Replaces the oldest page.
LRU (Least Recently Used): Replaces the page that has not been used for the longest time.
Optimal: Replaces the page that will not be used for the longest time in the future
Basic Functions of Memory Management
Tracking each byte of memory in the system.
Allocating and deallocating memory spaces as needed by the system's processes.
Managing swap spaces, which store inactive pages of memory.
Implementing policies for memory allocation.
Anam Maruf
Div-A
53003230032