


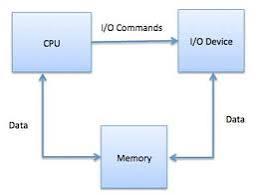
Memory input/output management refers to the processes that a computer or system uses to handle the flow of data between memory (storage) and input/output (I/O) devices like keyboards, monitors, and storage drives. It plays a crucial role in ensuring that data is efficiently read from or written to memory and devices, allowing for smooth operation of software and hardware.
Here are some key concepts:
1. Memory Management:
- Allocation/Deallocation: Dynamically assigning memory to processes and freeing it when no longer needed.
- Virtual Memory: Extending physical memory with disk space to handle larger tasks.
- Cache Management: Storing frequently accessed data in a high-speed memory section to speed up performance.
2. Input/Output Management:
- Device Drivers: Software components that allow the operating system to communicate with hardware devices.
- Buffering: Storing data temporarily in memory while it's being transferred between I/O devices and the system.
- Interrupt Handling:Mechanism where the I/O device signals the processor to handle I/O operations.
3. I/O Scheduling:
- Deciding the order in which I/O requests are processed to optimize performance.
In operating systems, effective memory and I/O management lead to faster response times, efficient use of resources, and overall system stability.