


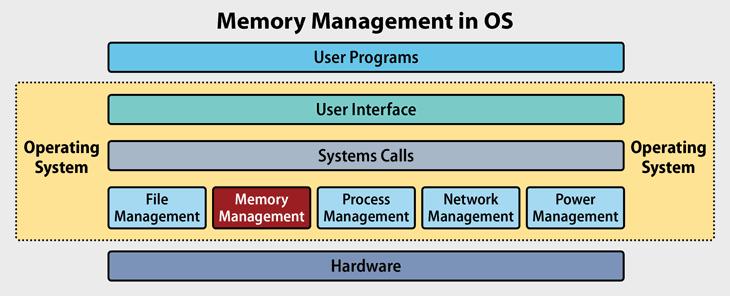
Memory Management:
Memory management is a crucial function of an operating system (OS) that handles the allocation and deallocation of memory resources. It ensures that each running process gets sufficient memory to execute, manages multiple processes by sharing memory efficiently, and protects memory spaces to prevent interference between processes. The OS also uses memory management techniques like paging and segmentation to optimize performance and prevent issues like fragmentation.
Virtual Memory:
Virtual memory is a memory management technique that allows an operating system to use hardware and software to compensate for physical memory shortages, effectively expanding the available memory. By using disk space as an extension of RAM, the OS can load and run larger applications or multiple programs simultaneously. Virtual memory enables processes to use more memory than physically available by swapping data between RAM and disk storage, allowing efficient multitasking and better system performance.