


Memory management is a vital and complex operating system task. It enables running multiple processes simultaneously without any interruptions. In operatinh systems, memory management is the function responsible foe managing the computer's primary memory. Memory management is the process os controlling and coordinating a computre's main memory. It ensures that blocks os memory space are proely managed and allocated so the porating system and other runing processes have the memory they need to carry out their poerations. Knowing how memory management in poerating systeam works is crucial for system stability and imroving system performance.
The memory management function keeps track of the status of each memory location, either allocated or free. It determines how memory is allocated among cometing processes, deciding wnich gets memory, when they receive it, and how much they are allowed. When memory is allocated it determines which memory locations will be assigned. It tracks when memory is freed or unallocated and upates the ststus.
To achieve a degree of multiprogramming and proer utilization of memory , memory management is important.many memory methods exist, reflecting various approaches, and the effectiveness of each algorithm depends on the situation.
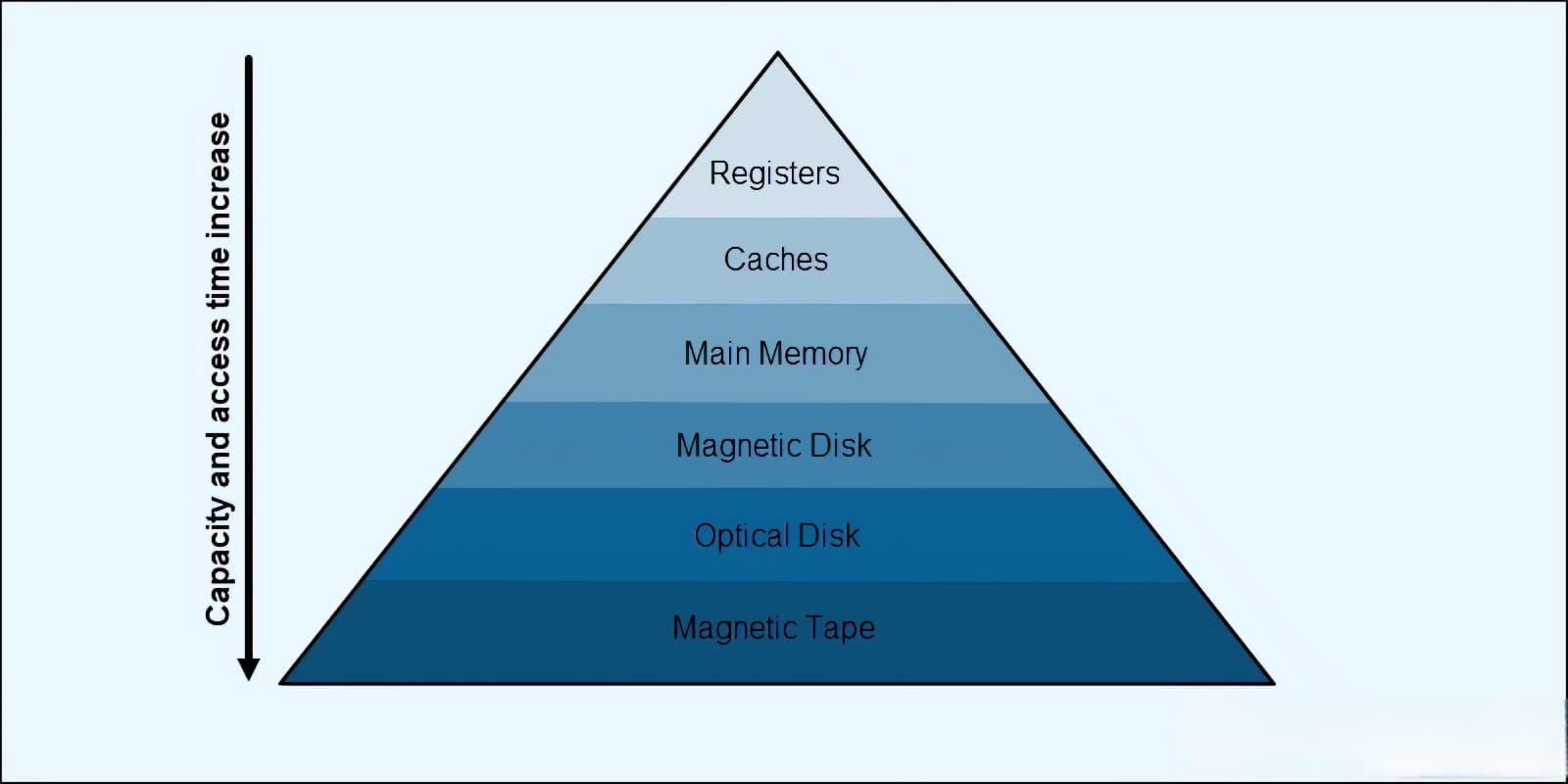
Several different memory types make up the memory unit. A computer's memory hierarchy and organization affect data speed and storage size. Faster and smaller caches are closer to the cpu, while larger and slower memory is further away.
The cpu regularly accesses data stored in memory. Efficient memory access infiuences how fast a cpu complettes tasks and becomes available foe new tasks. Memory access involves with addresses and defining access rules across memory levels.
Memory management balances tradeoffs between speed,size,and power use in a computer. Primary memeory allows fast access but no permanent storage. on the other hand, secondary memory is slower but offers permanent storage.