


An operating system is a type of software that acts as an interface between the user and the hardware. It is responsible for handling various critical functions of the computer and utilizing resources very efficiently so the operating system is also known as a resource manager. The operating system also acts like a government because just as the government has authority over everything, similarly the operating system has authority over all resources. Various tasks that are handled by OS are file management, task management, garbage management, memory management, process management, disk management, I/O management, peripherals management, etc.
generation of minicomputers saw a new phase of growth and development.
There are 4 type of generation in operating system
1. The First Generation (1940 to early 1950s)
In 1940, an operating system was not included in the creation of the first electrical computer. Early computer users had complete control over the device and wrote programs in pure machine language for every task. During the computer generation, a programmer can merely execute and solve basic mathematical calculations. an operating system is not needed for these computations.
2. The Second Generation (1955 – 1965)
GMOSIS, the first operating system (OS) was developed in the early 1950s. For the IBM Computer, General Motors has created the operating system. Because it gathers all related jobs into groups or batches and then submits them to the operating system using a punch card to finish all of them, the second-generation operating system was built on a single-stream batch processing system.
3. The Third Generation (1965 – 1980)
Because it gathers all similar jobs into groups or batches and then submits them to the second generation operating system using a punch card to finish all jobs in a machine, the second-generation operating system was based on a single stream batch processing system. Control is transferred to the operating system upon each job’s completion, whether it be routinely or unexpectedly. The operating system cleans up after each work is finished before reading and starting the subsequent job on a punch card. Large, professionally operated machines known as mainframes were introduced after that.
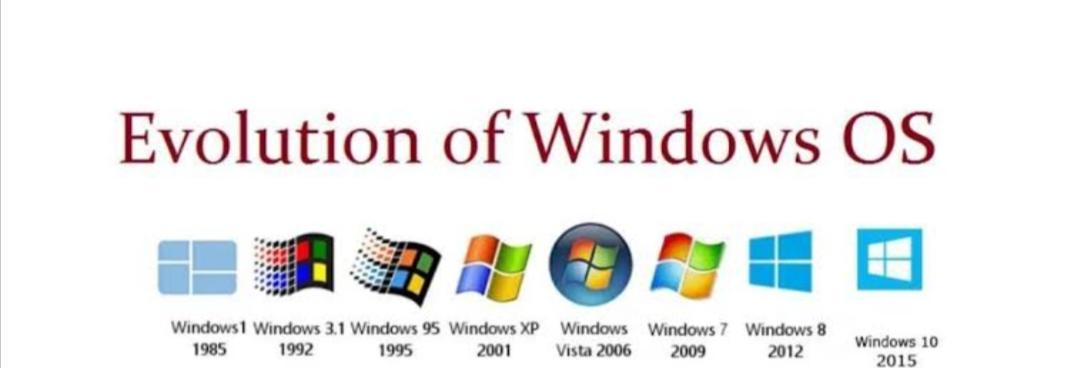
4.The Fourth Generation (1980 – Present Day)
The fourth generation of personal computers is the result of these PDPs. The Generation IV (1980–Present)The evolution of the personal computer is linked to the fourth generation of operating systems. Nonetheless, the third-generation minicomputers and the personal computer have many similarities. At that time, minicomputers were only slightly more expensive than personal computers, which were highly expensive.