


Topography is the study of the land surface. In particular, it lays the underlying foundation of a landscape. For example, topography refers to mountains, valleys, rivers, or craters on the surface. Elevation is the distinguishing factor for topographic maps.
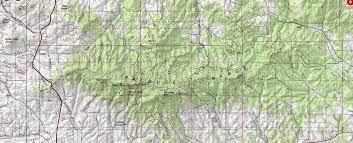
In GIS, we use digital elevation models for the terrain. Nine out of ten topographic maps show contour lines, which are just lines of equal elevation. The narrow definition of topography is specific to the arrangement of landforms.
But in a broader sense, it incorporates natural and artificial features. For example, topographic maps often tie in administrative boundaries, cities, hydrography, parks, landmarks, transportation, and buildings.
For the purposes of this article, topography specifically involves the recording of relief or terrain, the three-dimensional quality of the surface, and the identification of specific landforms. This is also known as geomorphometry. In modern usage, this involves generation of elevation data in electronic form. It is often considered to include the graphic representation of the landform on a map by a variety of techniques, including contour lines, Hypsometric tints, and relief shading