


DEADLOCK PREVENTION
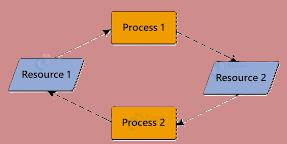
Deadlock is a situation in computing where two or more processes are unable to proceed because each is waiting for the other to release resources. Strategies used in computer systems in order to ensure that different processes can run smoothly without getting stuck waiting for each other forever is Deadlock prevention.
The deadlock has the following characteristics:
Deadlock can be prevented by ruling out any of the above four conditions:
Make data read only, so that processes can use the data concurrently. We know that many write procedure cannot take place at same time. Thus allow only exclusive users to writee into the file. And let others have access to read only.
The hold-and-wait condition can be prevented by requiring all processes to request for required access at a time. While doing so all other processes will be blocked until all requests are granted. This means that other non running processes will have to wait until their turn.
if a process requests for certain resources, it must release its original resources first. And if another process is using that resources it needs to release them
Each resource will have a numeric order. All processes must follow that order only while requesting resources. No process will be granted if they request for resources have higher priority than they have currently.
Thus in these ways deadlock can be prevented.