


Social media is one of the most readily accessible and powerful tools in this modern day and age. Many of us use our socials to stay in touch with our friends and family, or to keep up with the latest news in whatever we are interested in.
Social media is run by algorithms. It keeps tags on your activity and interactions to feed you the same type of content, over and over again. This is what we call a “filter bubble” because it filters everything that your activity does not align with and gives you everything that does.
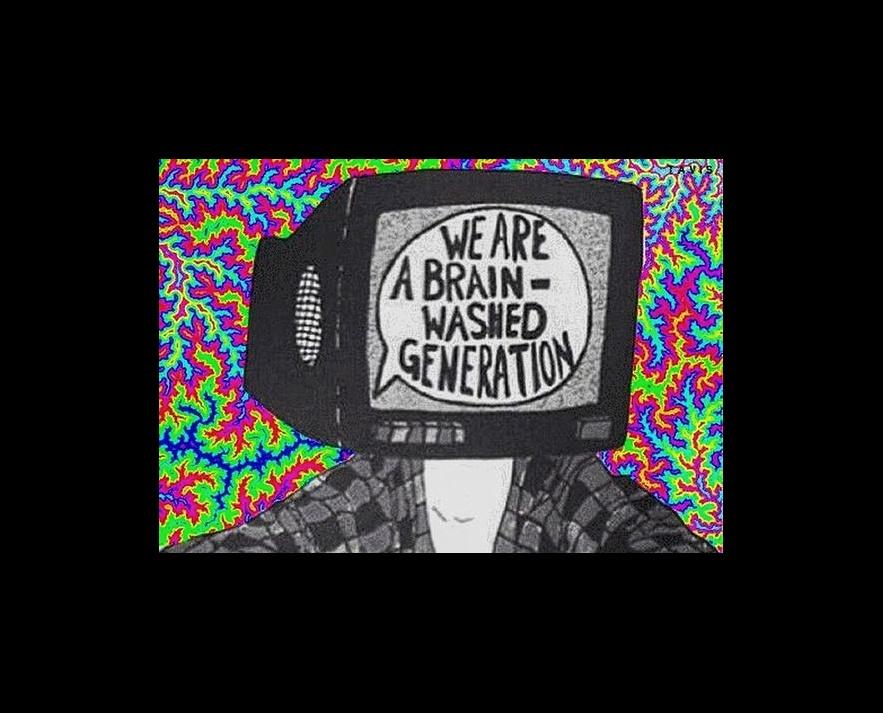
What does that have to do with brainwashing? Well, brainwashing stems from the act of exposing one to the same ideology over and over again, and if no one imposes them, they start to feed into it and believe that it is the most truthful idea. And though saying that social media can brainwash people can sound extreme, it is no secret that it is used to reinforce several brainwashing acts.
What does that have to do with brainwashing? Well, brainwashing stems from the act of exposing one to the same ideology over and over again, and if no one imposes them, they start to feed into it and believe that it is the most truthful idea. And though saying that social media can brainwash people can sound extreme, it is no secret that it is used to reinforce several brainwashing acts.
How can you know if you are brainwashed? Delusion, despite all the people telling you that you are wrong with supported and truthful evidence, is a huge red flag. If you find yourself getting very defensive over a topic that, when many others are telling you what you believe is wrong, and provide you with several solid pieces of evidence, that you even get disrespectful to them, know that you have fallen victim to brainwash.
To “cure” brainwashing and dismantle the false ideology does not happen overnight. So you must keep the conversation going, even if it takes over 70 years to completely dismantle the false ideology. It is our responsibility as social media users and human beings to fight against falsehood.