


Device Driver in computing refers to a special kind of software program or a specific type of software application that controls a specific hardware device that enables different hardware devices to communicate with the computer’s Operating System. A device driver communicates with the computer hardware by computer subsystem or computer bus connected to the hardware.
Device Drivers are essential for a computer system to work properly because, without a device driver, the particular hardware fails to work accordingly, which means it fails in doing the function/action it was created to do. Most use the term Driver, but some may say Hardware Driver, which also refers to the Device Driver
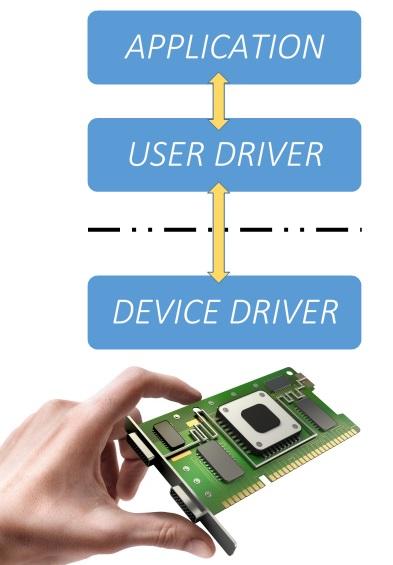
Device Drivers depend upon the Operating System’s instruction to access the device and perform any particular action. After the action, they also show their reactions by delivering output or status/message from the hardware device to the Operating system. For example, a printer driver tells the printer in which format to print after getting instruction from OS, similarly, A sound card driver is there due to which 1’s and 0’s data of the MP3 file is converted to audio signals and you enjoy the music. Card reader, controller, modem, network card, sound card, printer, video card, USB devices, RAM, Speakers, etc need Device Drivers to operate.