


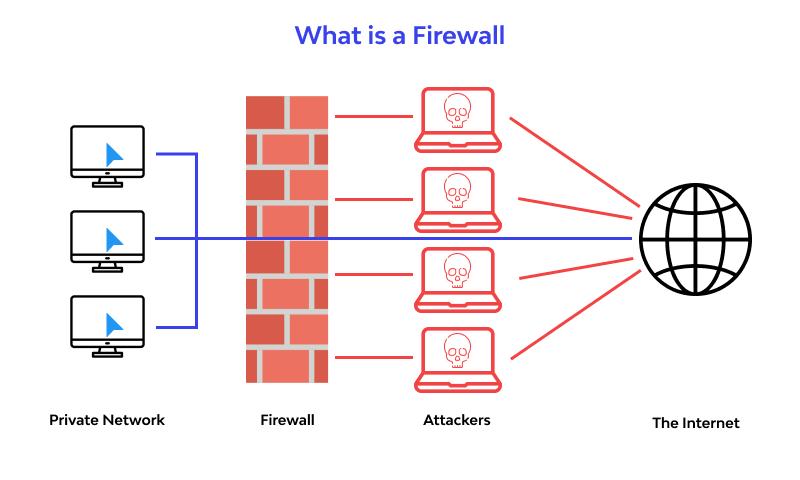
A simple explanation of what a Firewall is that it is hardware or software to protect a private computer or a network of computers. This protection is achieved with software or hardware or both to allow only authorized traffic and filter out all unauthorized users from accessing private computers and networks. A Firewall in a computer is a type of Cybersecurity tool. A Firewall in a computer is used for information security by detecting and blocking out all attempts at unsolicited access. Before venturing further, a beginner has to understand the basics of a Firewall and also know how does a Firewall work. A router in your home is a simple example to answer the query of what is a Firewall with an example. The Firewall in Win 10 is an answer to what is a Firewall in a computer.
An introduction to a Firewall is essential for a beginner. The purpose of a Firewall is to act as the first line of defense in network security. You can define a Firewall as a network security system that acts as a barrier between internal network and external sources like the internet to intercept and block data packets that don’t conform to its set of rules.
Firewall meaning, as the name suggests, is that it is a barrier to protect the computer systems and networks from outside attacks. The answer to the question ‘What is a Computer Firewall ?’ is that it is used to secure information from unauthorized users from both within the network and from outside networks. A beginner needs to understand Firewall basic concepts like what is meant by a Firewall or Firewall meaning in a computer.