


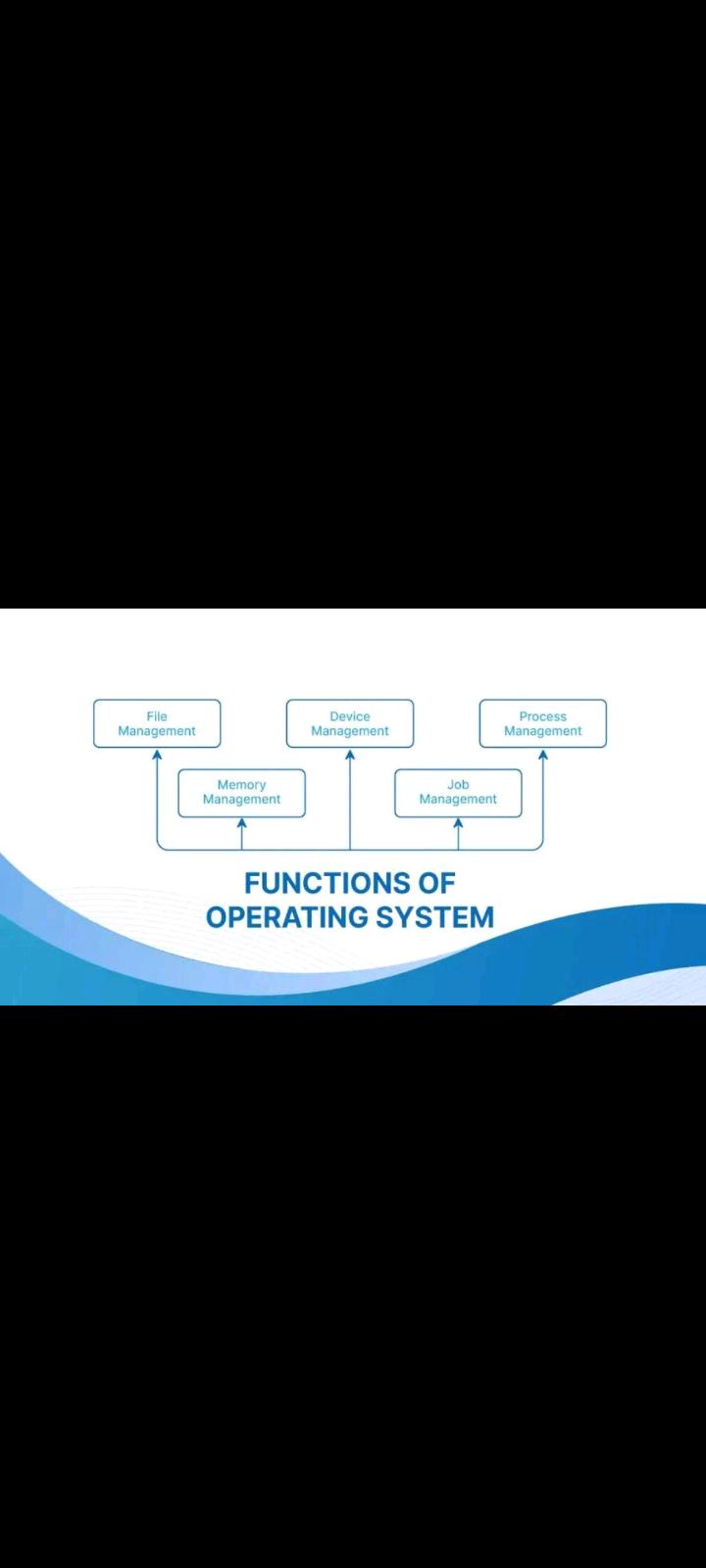
Functions of an Operating System
1. Memory Management
An Operating System performs the following activities for Memory Management:
• It keeps track of primary memory, i.e., which bytes of memory are used by which user program. The memory addresses that have already been allocated and the memory addresses of the memory that has not yet been used.
• In multiprogramming, the OS decides the order in which processes are granted memory access, and for how long.
• It Allocates the memory to a process when the process requests it and deallocates the memory when the process has terminated or is performing an I/O operation.
2. Process Management
An Operating System performs the following activities for Processor Management:
• An operating system manages the processor’s work by allocating various jobs to it and ensuring that each process receives enough time from the processor to function properly.
• Keeps track of the status of processes. The program which performs this task is known as a traffic controller.
• Allocates the CPU that is a processor to a process. De-allocates processor when a process is no longer required.
3. Device Management
An OS manages device communication via its respective drivers. It performs the following activities for device management:
• Keeps track of all devices connected to the system. Designates a program responsible for every device known as the Input/Output controller.
• Decide which process gets access to a certain device and for how long.
• Allocates devices effectively and efficiently. Deallocates devices when they are no longer required.
• There are various input and output devices. An OS controls the working of these input-output devices.
4. File Management
A file system is organized into directories for efficient or easy navigation and usage. These directories may contain other directories and other files. An Operating System carries out the following file management activities:
• It keeps track of where information is stored, user access settings, the status of every file, and more. These facilities are collectively known as the file system.
• An OS keeps track of information regarding the creation, deletion, transfer, copy, and storage of files in an organized way.
• It also maintains the integrity of the data stored in these files, including the file directory structure, by protecting against unauthorized access.
5. Protection and Security Management
The operating system uses password protection to protect user data and similar other techniques. it also prevents unauthorized access to programs and user data. The operating system provides various techniques which assure the integrity and confidentiality of user data. The following security measures are used to protect user data:
• Protection against unauthorized access through login.
• Protection against intrusion by keeping the firewall active.
• Protecting the system memory against malicious access.
• Displaying messages related to system vulnerabilities.