


Threads are like workers in an operating system. They help get things done faster by doing multiple tasks at the same time.
There are two main types of threads:
1. User-level threads: They are managed by the application itself and are quick to switch between tasks. However, they have some limitations in using system resources.
2. Kernel-level threads: These threads are managed by the operating system, and they can handle more tasks at once. They are better at using multiple CPU cores efficiently.
Think of it like this: User-level threads are like independent contractors hired by an application, and kernel-level threads are like employees directly managed by the operating system.
In terms of how they work together, there are different models:
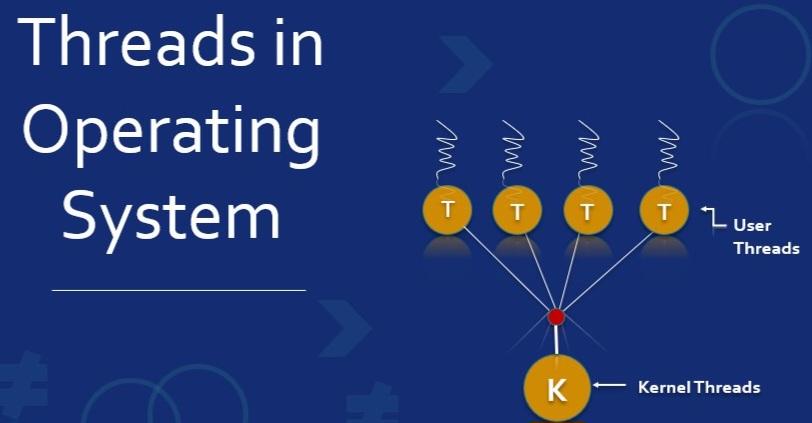
- Many-to-One Model: Multiple user-level threads are managed by a single kernel-level thread. This model is simple but lacks real parallelism.
- One-to-One Model: Each user-level thread is directly managed by a separate kernel-level thread. It offers true parallelism but can be resource-intensive.
- Many-to-Many Model: Multiple user-level threads are mapped to a smaller number of kernel-level threads, striking a balance between concurrency and resource usage.
The choice of thread type and model depends on the application's needs and the system's capabilities. So, threads help applications get things done faster and efficiently by doing tasks simultaneously.