


Kernel memory allocation in Linux refers to the way the operating system's core (the "kernel") manages and allocates memory for its internal processes and operations. Just like how programs running on your computer need memory to function, the kernel itself needs memory to handle tasks like managing files, running processes, and communicating with hardware.
In simple terms:
- Kernel Memory : This is a special area of memory reserved for the Linux kernel. It's separate from the memory used by regular applications.
- Allocation: When the kernel needs to perform a task (like starting a process or reading data from a disk), it "allocates" a portion of this memory for that task.
- Deallocation: After the task is done, the memory is freed up so it can be used for something else.
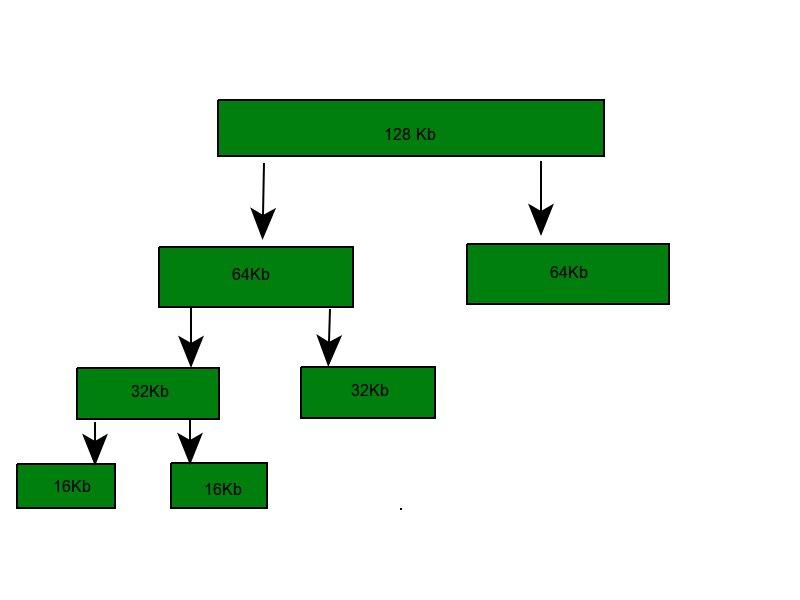
The kernel uses various techniques and structures to efficiently manage and allocate this memory, ensuring that the system runs smoothly and without crashes.