


Her legs are longer, her smile is brighter and even her teeth are whiter. We've all been there before; you're looking through a magazine and as you see yourself, you feel depressed because your hips are just too wide, your skin too blemished and your lips too thin to ever be one of these women. But no one can be because they don't exist. OK, so yes, the models are real people, but the image of them is not. These images have been edited more times than your text message to that guy you really like. Yet, we are still encouraged, no, told by the media that this is how we should look. This is what is beautiful. And apps like 'FaceTune' target us, showing us that using their face editing app we too can acquire such looks. But what happens when the phone isn't there and you see just you in the mirror. Does it feel enough?
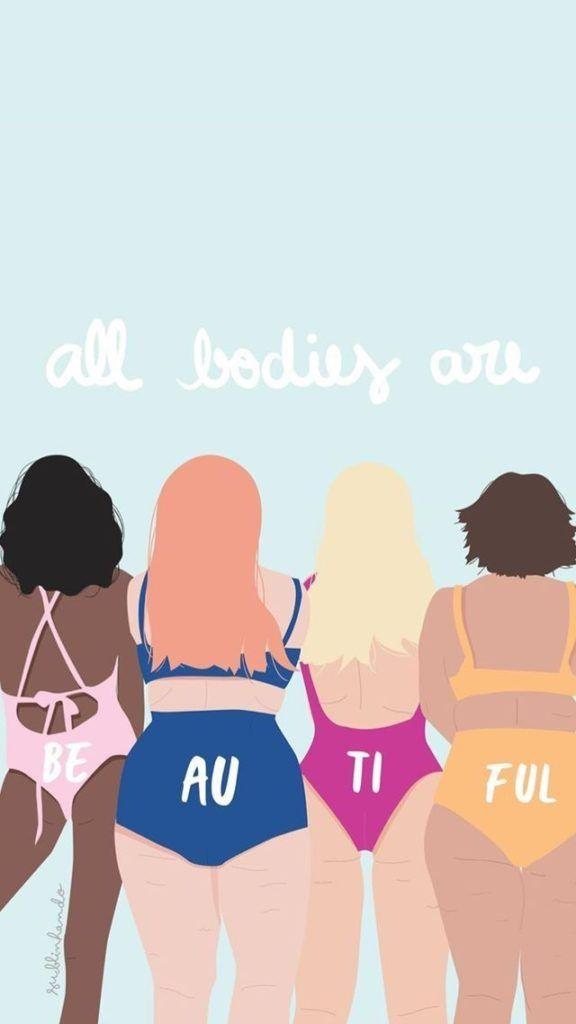
It should. Rather than blaming ourselves, starting crazy diets and cringing at every photo we're in, we need to stop trying to achieve these impossible standards of what is supposedly beautiful and embrace our own unique beauty. Beauty which means you may have got your big nose from your dad but it has been passed down from generation to generation like a family heirloom. Beauty which means a 'bikini body' is simply you in a bikini. Beauty which means you are not afraid to go out in the sun because it'll darken your skin, because this is part of who you are. And whether it's a freckle on your elbow or a birthmark on your back, it's almost like a physical stamp, your own personal trademark to say this is what makes me individual, what makes me, me! So, enjoy being you, smile at the world and let your unique beauty shine through.