


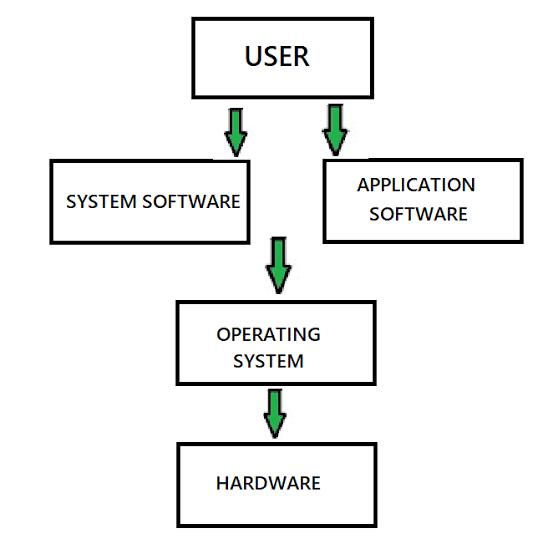
Contemporary operating systems or OS for short are a fundamental pillar of today’s computing environment because they act as the foundation for most applications and effectively handle the use of resources. An operating system is a layer of software that allows the user to interact with the computer hardware directly; it ensures smooth running and unparalleled efficiency of the entire process.
Multitasking is one of the important characteristics of contemporary operating systems, and it is aimed at the creation of conditions for the concurrent functioning of different applications which do not influence each other. This capability is important in boosting efficiency because users can move from one working task to the other and not have to open a new window or program. Through the implementations of managing, scheduling and allocating processes, and scheduling algorithms and techniques, operating systems facilitate multitasking.
Security is another serous consideration, which is a crucial pillar of the contemporary operating systems. Due to the modern threats associated with the use of computers and the Internet, the developers of OSs incorporate mechanisms for data and privacy protection. A user’s authentication, encryption, and access control are other characteristic that mitigate risks related to intrusion and malicious use. Updating must also be done on regular basis, and patches as well to handle various forms of vulnerabilities that may arise, to make the system safe.
Most of today’s operating systems are developed to be more friendly with a lot of easy to understand graphical user interfaces the GUIs. GUIs enable the user to interact with the system in a very efficient way despite the task complicity by employing elements such as windows, icons, and menus. This concern with usability also applies to its accessibility features computers so that persons with disabilities will be able to effectively use them.
Today we are dealing with a number of technologies and this makes compatibility and interoperability an important affair. Most current operating systems work cooperatively with numerous types of the hardware devices and software applications that are allowed to function and interact with the system. There is a use of standard form and APIs/Appl Programming Interfaces for integration of the disparate systems.