


Operating System is an integrated essential program that enables the functioning of the computer’s hardware and software resources, as well as provision of common services to various computer programs. It facilitates smooth running of tasks and resource allocation between users and computer hardware.
Enables programming scheduling and coordination.
Takes care of memory assignment and release for different processes.
Data storage in form of files is organized, saved, searched, and manipulated.
Controls and manages all types of hardware devices through drivers.
User interaction through CLI or GUI.
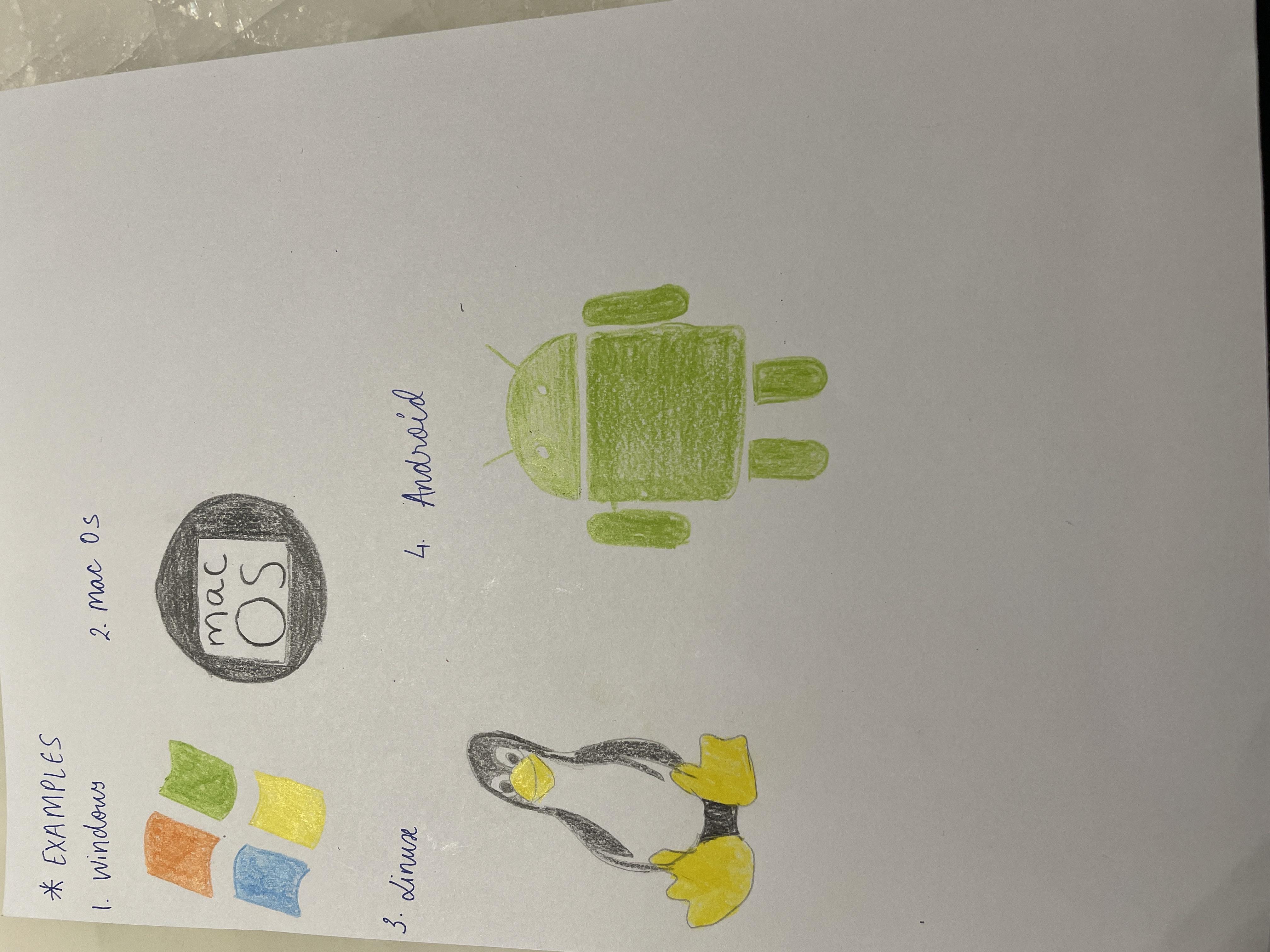
This operating system was created by Microsoft has become popular on personal computers because it has a friendly graphical user interface (GUI), supports many applications; examples include Windows 10, Windows 11.
The Macintosh Operating System developed by Apple which is known for its sleek design as well as seamless integration with other apple products; examples include macOS Ventura, macOS Monterey.
It is an open-source operating system known for its stability and security making it popular in servers or supercomputers; these include Ubuntu, Fedora, Debian etc.
An OS developed by Google being the most used as a dominant server for smartphones and tablets.