


VIRTUAL MEMORY
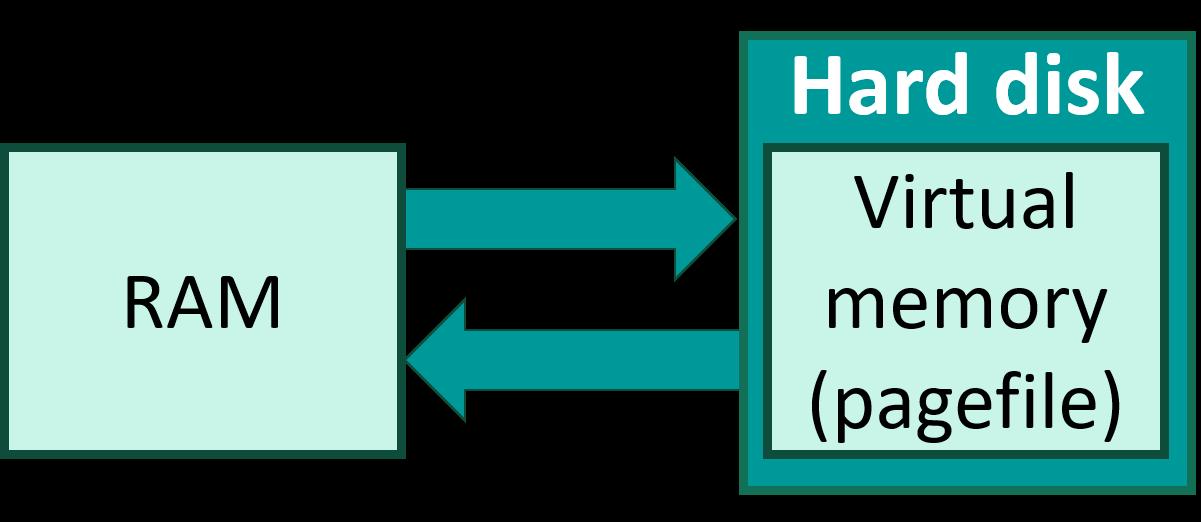
Introduction: Virtual memory is a crucial concept in modern operating systems, allowing them to manage and utilize physical memory (RAM) more efficiently. It enables a computer to compensate for physical memory shortages, by temporarily transferring data from random access memory (RAM) to disk storage.
Key concepts :
Paging: Divides virtual memory into small blocks called pages, which are mapped to physical memory as needed.
Page Table: A data structure that maps virtual addresses to physical addresses.
Page Fault: Occurs when a program accesses a page not currently in RAM, prompting the OS to load it from disk.
Swapping: Moves inactive pages from RAM to disk to free up memory for other processes.
Thrashing: When excessive swapping degrades system performance.
Benefits of Virtual Memory:
Isolation and Security: Virtual memory provides each process with its own isolated memory space, preventing one process from accessing or corrupting another's memory.
Efficient Memory Utilization: Virtual memory allows the OS to use physical memory more efficiently, allocating memory to processes as needed and swapping out inactive pages.
Support for Large Applications: Programs can use more memory than what is physically available, as the OS can load and unload parts of the program as needed.