


Scheduling tweets is one of the best ways to streamline your content planning, and not to mention, it’s a huge time-saver.
You can prep all of your tweets in one super-productive session, so you’re not scrambling to post on-the-fly.
That way on consistent basis you can creating a more and stress-free approach to your social media strategy.
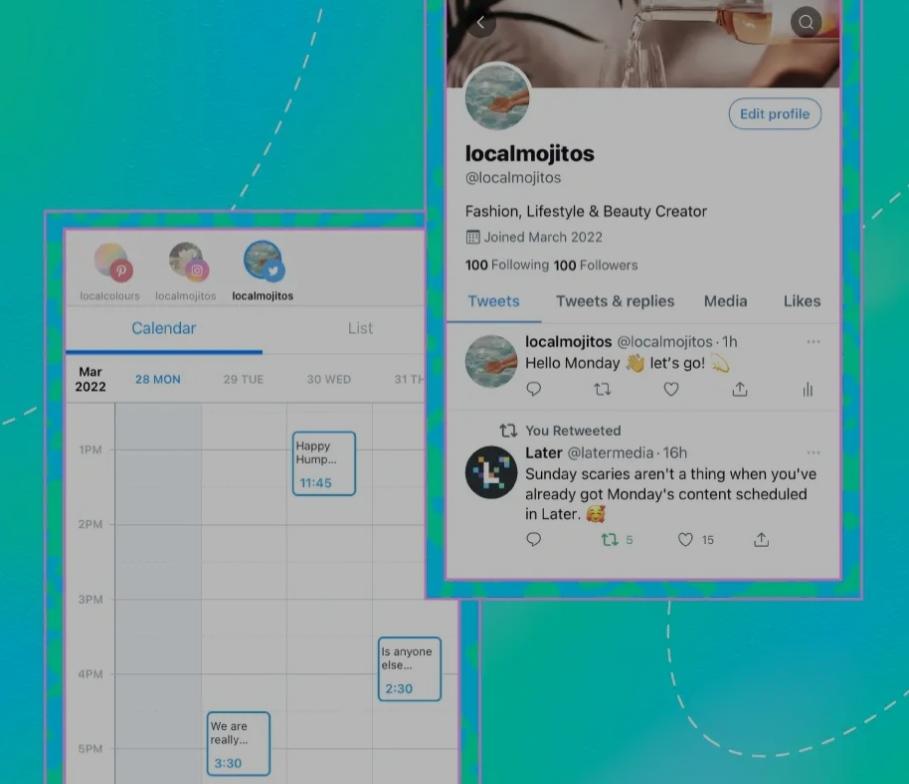
With Later, you can plan and schedule Twitter posts alongside all your other social media channels — including Instagram, Facebook, Pinterest, TikTok, and LinkedIn — saving you valuable time and effort.
Ofyou more information on how to Schedule Tweets on Twitter then please refer the following link: https://later.com/blog/how-to-schedule-tweets/