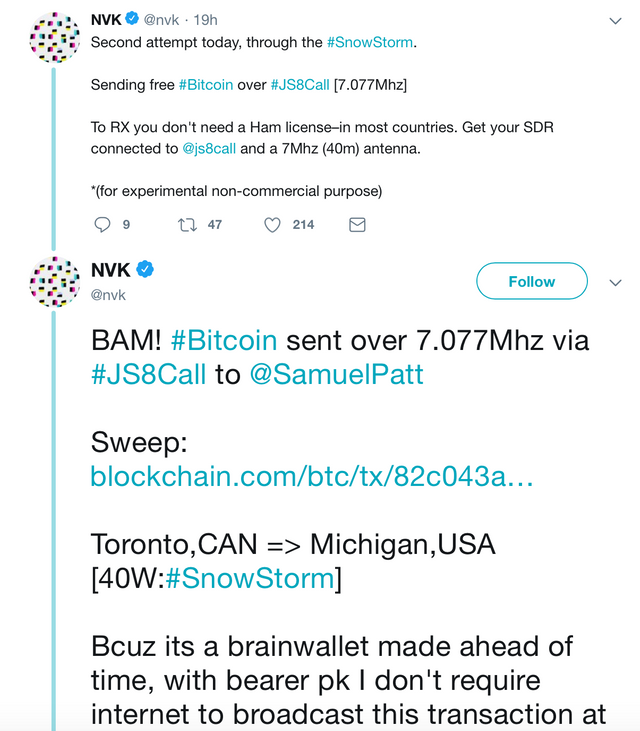
The decentralized blockchain keeps amazing us with the endless possibilities and potential that it have under the hood. Right from the highest hit of BTC/USD people are showing more interest in crypto and want to become a part of this world too. However, regulation is needed to ensure the safety of the stake that a user is putting in the economy. The biggest news is coming from the USA where the bitcoin is sent over radio waves in absence of internet. This was a non-commercial experiment carried out on a 7 Mhz frequency. This ensures the future of both bitcoin and the crypto market.
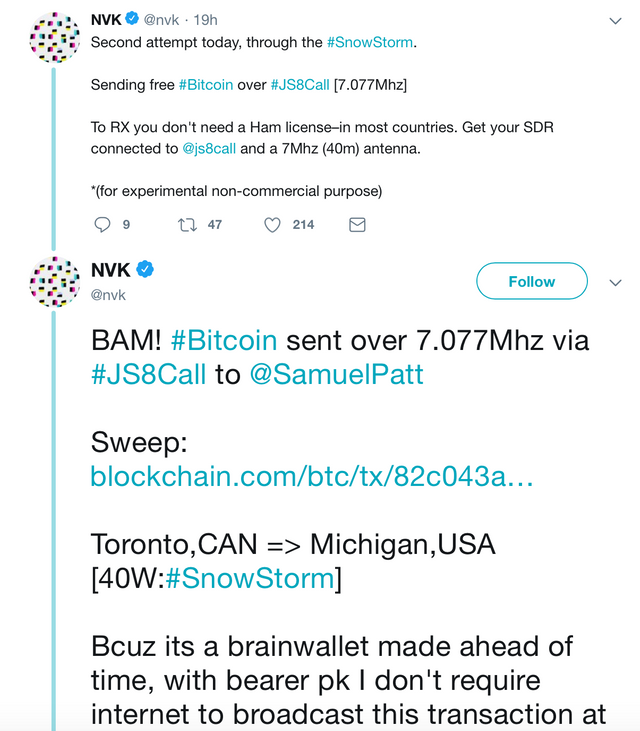
More details on the official twitter handle => https://twitter.com/nvk/status/1095354354289135617
Direct link to the transaction happened using radio waves => https://www.blockchain.com/btc/tx/82c043a82770e9129633d2c7259818b404d467fb8cab963773c574857a96202e




 More details on the official twitter handle => https://twitter.com/nvk/status/1095354354289135617
Direct link to the transaction happened using radio waves => https://www.blockchain.com/btc/tx/82c043a82770e9129633d2c7259818b404d467fb8cab963773c574857a96202e
More details on the official twitter handle => https://twitter.com/nvk/status/1095354354289135617
Direct link to the transaction happened using radio waves => https://www.blockchain.com/btc/tx/82c043a82770e9129633d2c7259818b404d467fb8cab963773c574857a96202e