


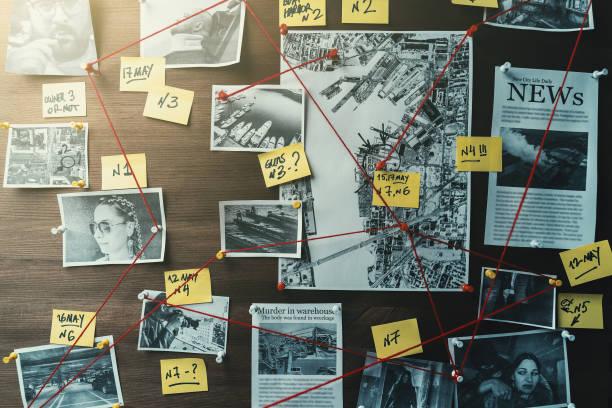
To preserve the state of the digital objects at the digital crime scene, the crime scene is searched for evidence. The goal of this phase is to recognize the digital objects that may contain information about the incident.
The first phase is to define a target that will be used to locate the evidence. For example, if you are looking for a file named foo.txt, then the target would have a name of foo.txt. If you are looking for a file with “bar” in the content, then the target would have “bar” in the content.
Second phase is to extract data from the crime scene in some search pattern.
Third phase is to compare the extracted data with the target. After new evidence is found
Fourth phase updates the general knowledge about the investigation so that more targets can be defined.
The phases have been organized into the basic requirements of an investigation: namely that we need to search for evidence that shows the causes and effects of an event and we need to develop hypotheses about the events that occurred at the crime scene. Each phase has a clear goal and requirements and procedures can be developed accordingly. We have also clearly outlined the definitions and concepts that were used in this framework. Choosing a process model is a subjective process and there will likely never be an agreement on a single model. Each must be evaluated with respect to how it can scale for future technologies and how it can handle different types of investigations.