In Operating Systems, concurrency refers to the ability of multiple processes to execute simultaneously, sharing common resources such as CPU time, memory, and I/O devices. However, this concurrency can lead to two major problems: Deadlock and Starvation.
Deadlock:
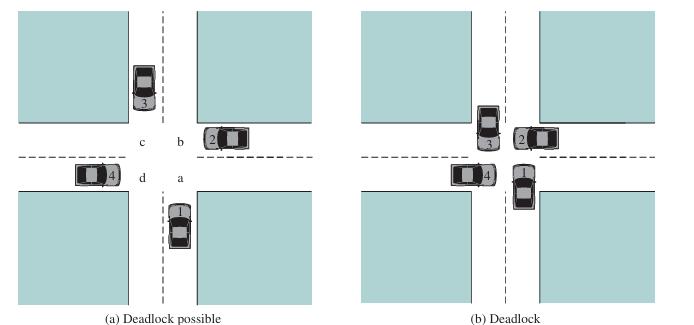
A deadlock is a situation where two or more processes are blocked indefinitely, each waiting for the other to release a resource. This occurs when the following four conditions are met:
- Mutual Exclusion: Two or more processes require exclusive access to a common resource.
- Hold and Wait: A process holds a resource and waits for another resource, which is held by another process.
- No Preemption: The operating system cannot preempt a process holding a resource.
- Circular Wait: A circular chain of processes exists, where each process waits for a resource held by the next process in the chain.
Starvation:
Starvation is a situation where a process is unable to gain access to a shared resource and is indefinitely postponed. This occurs when a process is waiting for a resource that is being held by another process, and the waiting process is not given a chance to execute.
Causes of Starvation:
- Priority Scheduling: A process with a lower priority may be starved of CPU time if a higher-priority process is always running.
- Resource Constraints: A process may be starved of a resource if another process is holding onto it for an extended period.
- Scheduling Algorithms: Certain scheduling algorithms, such as First-Come-First-Served (FCFS), can lead to starvation.
Prevention of Deadlock and Starvation:
To prevent deadlock and starvation, operating systems use various techniques, including:
- Resource Ordering: Ordering resources to prevent circular waits.
- Banker's Algorithm: A resource allocation algorithm that prevents deadlock.
- Priority Ceiling Protocol: A protocol that prevents starvation by assigning a priority ceiling to each resource.
- Scheduling Algorithms: Using scheduling algorithms that prevent starvation, such as Round Robin (RR) and Multilevel Feedback Queue (MFQ).