


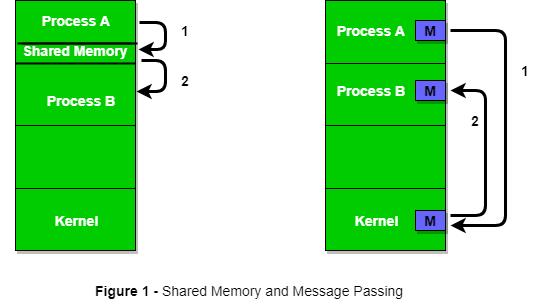
Message Passing
When processes interact with one another, two fundamental requirements must be satisfied: synchronization and communication. Processes need to be synchronized to enforce mutual exclusion; cooperating processes may need to exchange information. One approach to providing both of these functions is message passing. Message passing has the further advantage that it lends itself to implementation in distributed systems as well as in shared-memory multiprocessor and uniprocessor systems.
Message-passing systems come in many forms. In this section, we provide a general introduction that discusses features typically found in such systems. The actual function of message passing is normally provided in the form of a pair of primitives:
send (destination, message)
` receive (source, message)
This is the minimum set of operations needed for processes to engage in message passing. A process sends information in the form of a message to another process designated by a destination . A process receives information by executing the receive primitive, indicating the source and the message .
Synchronisation:
The communication of a message between two processes implies some level of synchronization between the two: The receiver cannot receive a message until it has been sent by another process. In addition, we need to specify what happens to a process after it issues a send or receive primitive.
Consider the send primitive first. When a send primitive is executed in a process, there are two possibilities: Either the sending process is blocked until the message is received, or it is not. Similarly, when a process issues a receive primitive, there are two possibilities:
1. If a message has previously been sent, the message is received and execution continues.
2. If there is no waiting message, then either
(a) the process is blocked until a message arrives, or
(b) the process continues to execute, abandoning the attempt to receive.