


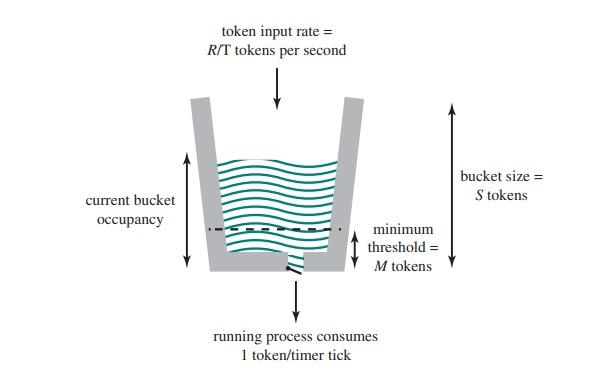
In the Linux VServer virtual machine (VM) facility, the allocation of processor time to multiple VMs is managed using a Token Bucket Filter (TBF). This system ensures that each VM receives a fair share of processing resources, particularly in environments with single or multicore processors.
Fraction of Processor Allocation
Processor Allocation Formula: The ratio of token generation rate (R) to the time interval (T) determines the fraction of a single processor's capacity allocated to a VM:
R/T = Fraction of processor allocation
Linux VServer Token Bucket Scheme
For example, in a system with four cores, if a VM is intended to use the equivalent of one full core, R is set to 1, and T is set to 4.
Overall System Limitation: The total fraction of processor time allocated to all VMs should not exceed the available processing power. If there are N VMs, the sum of their allocations must satisfy
Setting Parameters: S and M
M=W*H*R/T
S=W×B×(1−R/T)
Example Calculation:
M=1,000×5×0.5=2,500 tokens
S=1,000×30×(1−0.5)=15,000 tokens
Significance
These formulas and parameters allow for precise control over how much processor time a VM can use and how long it must wait before resuming after depleting its allocated tokens. This ensures fair resource distribution and prevents any VM from monopolizing the CPU.
Conclusion
The TBF mechanism in Linux VServer is critical for managing processor allocation in environments with multiple VMs. By carefully configuring the parameters R, T, S, and M, system administrators can control VM behavior during bursts of activity, ensuring that all VMs receive their fair share of CPU time without overwhelming the system.