


IT Service is providing value to the customer just as the other services
Here's a breakdown:
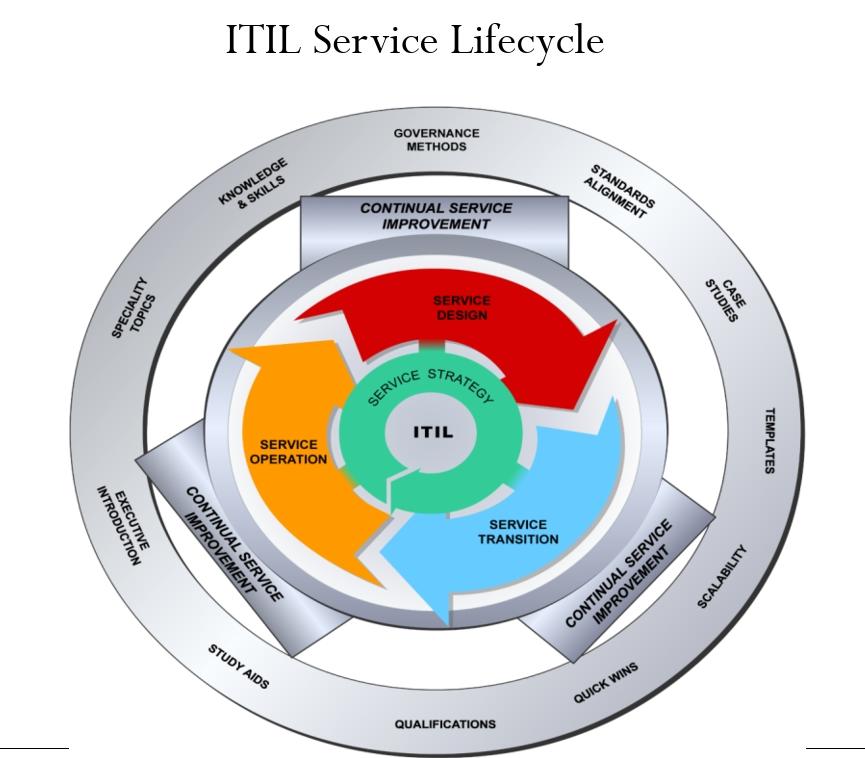
Service Strategy: Dreaming up the perfect IT service.
Defining the service: What problem does it solve? Who needs it?
Aligning with business goals: How does it help the company achieve its objectives?
Financial planning: How much will it cost? What's the return on investment?
Service Design: Sketching out the details.
Designing the service: How will it work? What technologies will it use?
Creating processes: How will it be delivered and managed?
Developing documentation: Clear instructions for everyone involved.
Service Transition: Making it a reality.
Planning the transition: How will the old system be replaced with the new one?
Testing and validation: Ensuring everything works as expected.
Training and knowledge transfer: Equipping staff with the necessary skills.
Deployment: Rolling out the new service to users.
Service Operation: Keeping the party going.
Delivering the service: Ensuring it's available and performing as expected.
Request fulfillment: Handling user requests and changes.
Continual Service Improvement: Learning from the experience.
Implementing changes: Making necessary adjustments to the service.
Imagine you're planning a grand party. You start by dreaming up the perfect event (Service Strategy), sketching out the details like guest list, menu, and decorations (Service Design), and then meticulously arrange everything, from invitations to catering (Service Transition).
On the big day, you ensure everything runs smoothly, guests are happy, and any hiccups are quickly resolved (Service Operation). After the party, you reflect on what worked, what didn't, and what you'd do differently next time (Continual Service Improvement).
Just like a well-planned party, a well-managed IT service lifecycle ensures a smooth experience for users, minimal disruptions, an
d continuous improvement.