1. Babel Fish earbuds

Named for the science-fiction comedy concept introduced by Douglas Adams in The Hitchhiker’s Guide To The Galaxy, these are earbuds utilizing instant online translation technology, effectively letting humans understand each other while communicating in different languages, in near real-time. Rotman says “Google’s Pixel Buds mean that people can easily carry out a natural conversation with someone speaking a different language.”Although the ear buds themselves are still at an early stage and, reportedly, do not yet function too well, anyone can access the underlying technology today through Google’s voice-activated translation services on computers and mobile devices.
2. Genetic Fortune Telling

Huge advances are being made in predictive analytics using genomic data by players including Helix, 23andMe, Myriad Genetics, BK Biobank and the Broad Institute. This is making is possible to predict chances of diseases such as cancer, or even IQ, by analyzing genetic data. This promises to be the next quantum leap in public health protection, but also raises huge ethical concerns, including the risk of genetic discrimination.“Genetic fortune telling will make it possible to predict the chances that you’ll be smart or below average in intelligence. It will also make it possible to predict behavior traits. But how will we use that information? Will it change how we educate children and judge their potential?” Though the new DNA tests offer probabilities, not diagnoses, they could greatly benefit medicine. For example, if women at high risk for breast cancer got more mammograms and those at low risk got fewer, those exams might catch more real cancers and set off fewer false alarms.
3. 3D Metal Printing
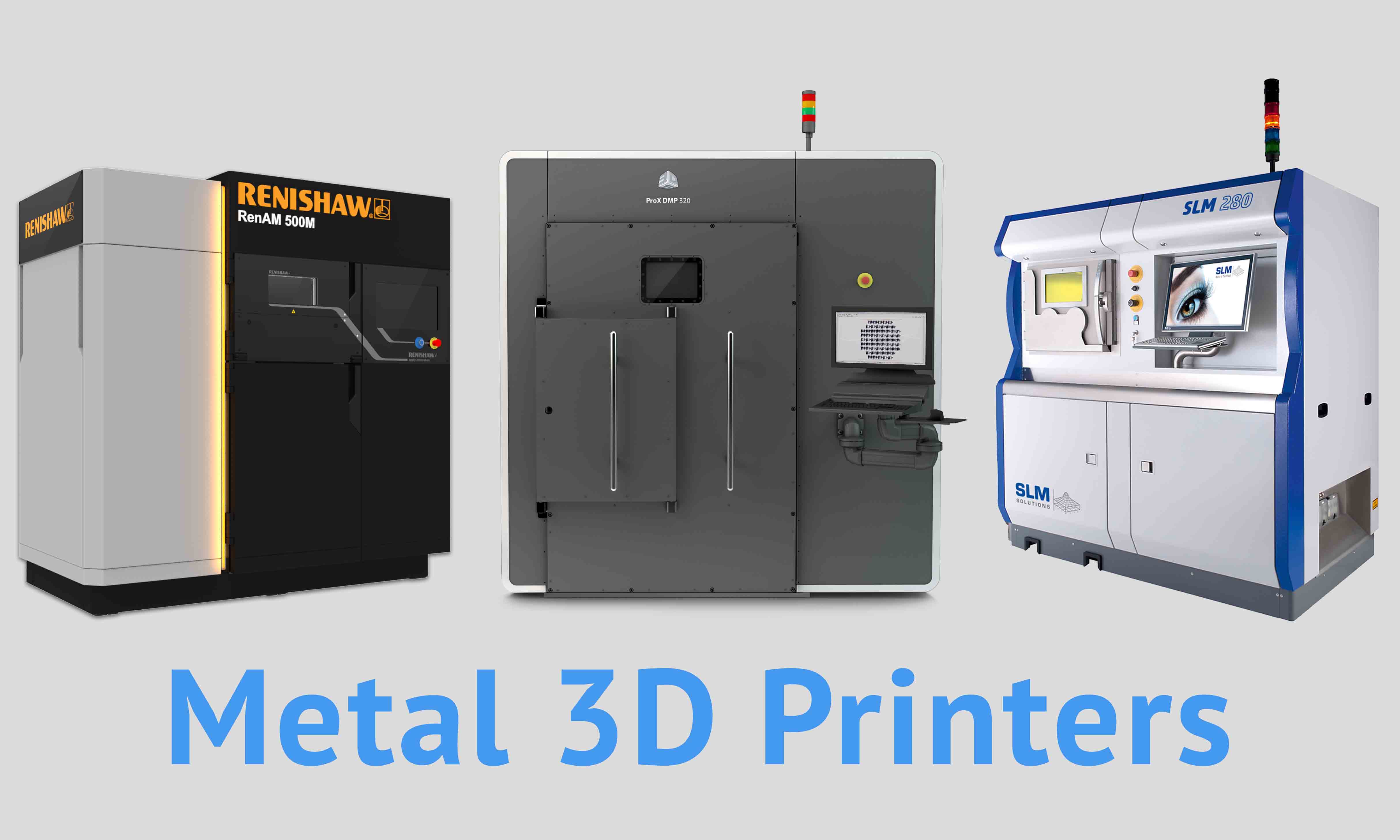
“3D metal printing gives manufacturers the ability to make a single or small number of metal parts much more cheaply than using existing mass-production techniques,” Rotman says. “Instead of keeping a large inventory of parts, the company can simply print a part when the customer needs it. Additionally, it can make complex shapes not possible with any other method. That can mean lighter or higher performance parts.”
4. Perfecting Online Privacy

Blockchain-based privacy systems make it possible for digital transactions to be recorded and validated while protecting the privacy of the information and identities underlying the exchange of information. This means it is easier to disclose information without risking privacy or exposure to threats such as fraud or identity theft. The tool is an emerging cryptographic protocol called a zero-knowledge proof. Though researchers have worked on it for decades, interest has exploded in the past year, thanks in part to the growing obsession with cryptocurrencies, most of which aren’t private.
5. Dueling Neural Networks
“Dueling Neural Networks describes a breakthrough in artificial intelligence that allows AI to create images of things it has never seen. It gives AI a sense of imagination,” says Rotman. However, he also urges caution, as it raises the possibility of computers becoming alarmingly capable tools for digital fakery and fraud. The technology has become one of the most promising advances in AI in the past decade, able to help machines produce results that fool even humans.



 Named for the science-fiction comedy concept introduced by Douglas Adams in The Hitchhiker’s Guide To The Galaxy, these are earbuds utilizing instant online translation technology, effectively letting humans understand each other while communicating in different languages, in near real-time. Rotman says “Google’s Pixel Buds mean that people can easily carry out a natural conversation with someone speaking a different language.”Although the ear buds themselves are still at an early stage and, reportedly, do not yet function too well, anyone can access the underlying technology today through Google’s voice-activated translation services on computers and mobile devices.
2. Genetic Fortune Telling
Named for the science-fiction comedy concept introduced by Douglas Adams in The Hitchhiker’s Guide To The Galaxy, these are earbuds utilizing instant online translation technology, effectively letting humans understand each other while communicating in different languages, in near real-time. Rotman says “Google’s Pixel Buds mean that people can easily carry out a natural conversation with someone speaking a different language.”Although the ear buds themselves are still at an early stage and, reportedly, do not yet function too well, anyone can access the underlying technology today through Google’s voice-activated translation services on computers and mobile devices.
2. Genetic Fortune Telling
 Huge advances are being made in predictive analytics using genomic data by players including Helix, 23andMe, Myriad Genetics, BK Biobank and the Broad Institute. This is making is possible to predict chances of diseases such as cancer, or even IQ, by analyzing genetic data. This promises to be the next quantum leap in public health protection, but also raises huge ethical concerns, including the risk of genetic discrimination.“Genetic fortune telling will make it possible to predict the chances that you’ll be smart or below average in intelligence. It will also make it possible to predict behavior traits. But how will we use that information? Will it change how we educate children and judge their potential?” Though the new DNA tests offer probabilities, not diagnoses, they could greatly benefit medicine. For example, if women at high risk for breast cancer got more mammograms and those at low risk got fewer, those exams might catch more real cancers and set off fewer false alarms.
3. 3D Metal Printing
Huge advances are being made in predictive analytics using genomic data by players including Helix, 23andMe, Myriad Genetics, BK Biobank and the Broad Institute. This is making is possible to predict chances of diseases such as cancer, or even IQ, by analyzing genetic data. This promises to be the next quantum leap in public health protection, but also raises huge ethical concerns, including the risk of genetic discrimination.“Genetic fortune telling will make it possible to predict the chances that you’ll be smart or below average in intelligence. It will also make it possible to predict behavior traits. But how will we use that information? Will it change how we educate children and judge their potential?” Though the new DNA tests offer probabilities, not diagnoses, they could greatly benefit medicine. For example, if women at high risk for breast cancer got more mammograms and those at low risk got fewer, those exams might catch more real cancers and set off fewer false alarms.
3. 3D Metal Printing
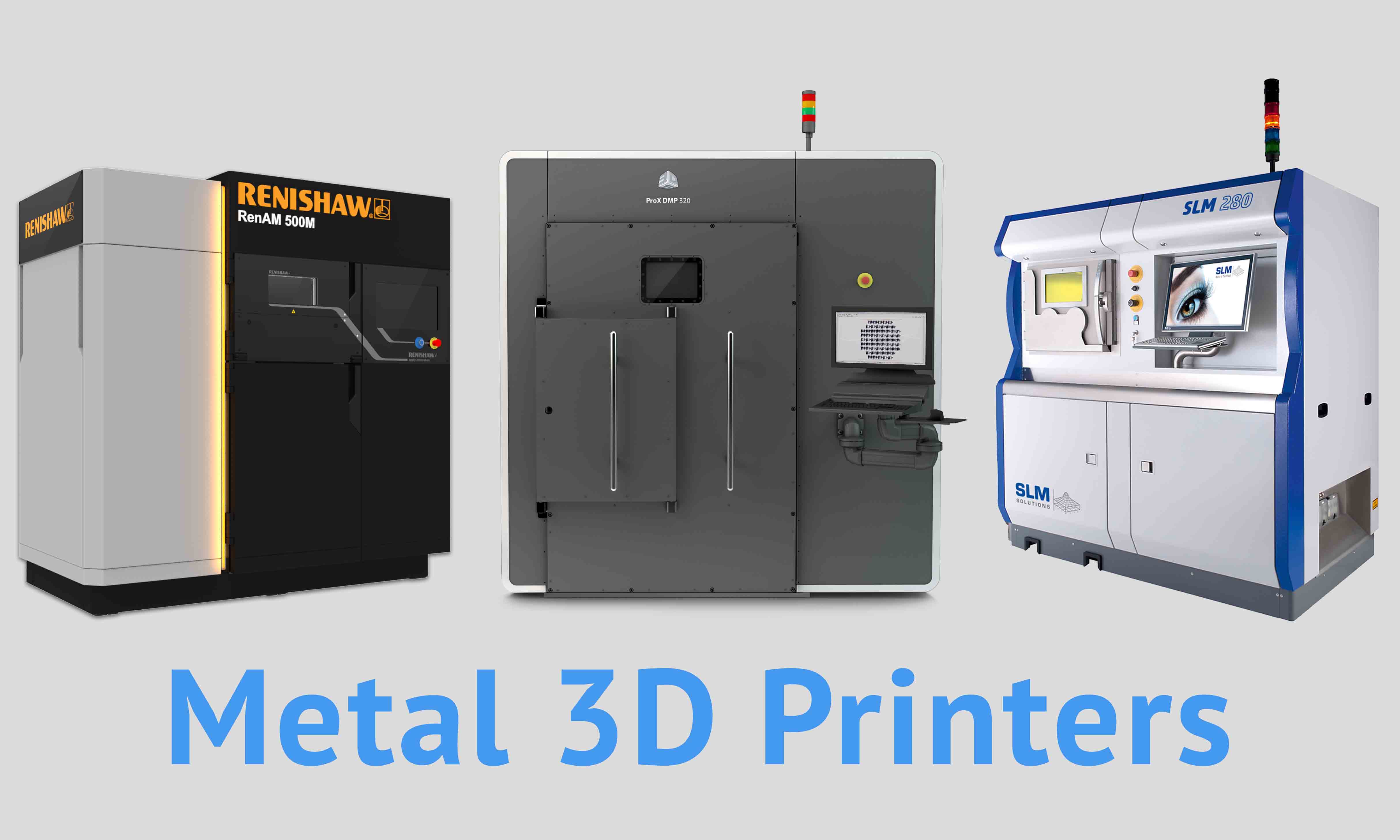 “3D metal printing gives manufacturers the ability to make a single or small number of metal parts much more cheaply than using existing mass-production techniques,” Rotman says. “Instead of keeping a large inventory of parts, the company can simply print a part when the customer needs it. Additionally, it can make complex shapes not possible with any other method. That can mean lighter or higher performance parts.”
4. Perfecting Online Privacy
“3D metal printing gives manufacturers the ability to make a single or small number of metal parts much more cheaply than using existing mass-production techniques,” Rotman says. “Instead of keeping a large inventory of parts, the company can simply print a part when the customer needs it. Additionally, it can make complex shapes not possible with any other method. That can mean lighter or higher performance parts.”
4. Perfecting Online Privacy
 Blockchain-based privacy systems make it possible for digital transactions to be recorded and validated while protecting the privacy of the information and identities underlying the exchange of information. This means it is easier to disclose information without risking privacy or exposure to threats such as fraud or identity theft. The tool is an emerging cryptographic protocol called a zero-knowledge proof. Though researchers have worked on it for decades, interest has exploded in the past year, thanks in part to the growing obsession with cryptocurrencies, most of which aren’t private.
5. Dueling Neural Networks
Blockchain-based privacy systems make it possible for digital transactions to be recorded and validated while protecting the privacy of the information and identities underlying the exchange of information. This means it is easier to disclose information without risking privacy or exposure to threats such as fraud or identity theft. The tool is an emerging cryptographic protocol called a zero-knowledge proof. Though researchers have worked on it for decades, interest has exploded in the past year, thanks in part to the growing obsession with cryptocurrencies, most of which aren’t private.
5. Dueling Neural Networks
 “Dueling Neural Networks describes a breakthrough in artificial intelligence that allows AI to create images of things it has never seen. It gives AI a sense of imagination,” says Rotman. However, he also urges caution, as it raises the possibility of computers becoming alarmingly capable tools for digital fakery and fraud. The technology has become one of the most promising advances in AI in the past decade, able to help machines produce results that fool even humans.
“Dueling Neural Networks describes a breakthrough in artificial intelligence that allows AI to create images of things it has never seen. It gives AI a sense of imagination,” says Rotman. However, he also urges caution, as it raises the possibility of computers becoming alarmingly capable tools for digital fakery and fraud. The technology has become one of the most promising advances in AI in the past decade, able to help machines produce results that fool even humans.