


Buffers:
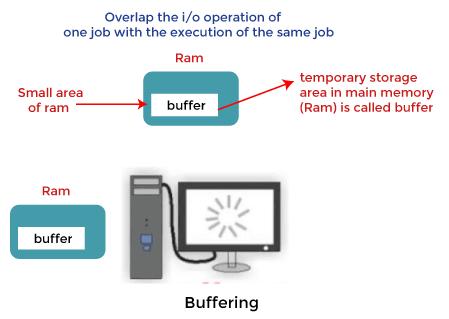
A buffer is a temporary storage space reserved in memory used to hold data while its being transferred between two devices/ processes.
Buffer plays important role in managing difference in data process speeds and allows for efficient data transfer.
Need for Buffers:
1. Differences in speed:
Devices in computer operates at different speeds.(Example, CPU is faster than Hard Drive). CPU have to wait for the slower device leading to inefficient usage.
A buffer stores data from the faster device temporarily and allows the slower device to process the data from the buffer at its own speed.
2. Data Stream Handling:
In stream-oriented connection, data transmits in continuous flow. The data transmits at different speed at different times.
Sometimes data arrives at faster intervals that the system cannot handle it.
Buffer solve problem by storing it while the system processes the data sequentially.
3. Temporary Storage:
Buffers help in temporary storing the data when the receiving system is not ready or cannot process entire data.
Buffers temporary hold the data and this allows the receiving system to process it later when its available back.
Types of Buffers:
1. Single Buffer:
A single buffer is a simple type of buffer that uses a fixed amount of memory to store data temporarily.
The buffer is stored with data and once its full, it waits for data to get processed/ transferred before its refilled.
Single buffer is most basic type of buffer and is simple for implement for basic I/O operations.
2. Double Buffer:
In double buffer systems, two buffers are used. When one buffer is filled the data, the system processes its data. The second is used to handle incoming data from input devices while the data from the first buffer is being processed.
Reduces waiting time and allows for continuous data transfer by overlapping I/O phases.
However, requires more memory compared to single buffer.
3. Circular Buffer:
A Circular buffer also known as Ring Buffer is a buffer of fixed size in which the write pointer wraps back to the start when the buffer reaches the end.
There is no need to reset or move data completely from the buffer and is suitable for real time applications as buffer is reused continuously.
If new data is to old data may be overwritten or halt operation until space is freed for further data.