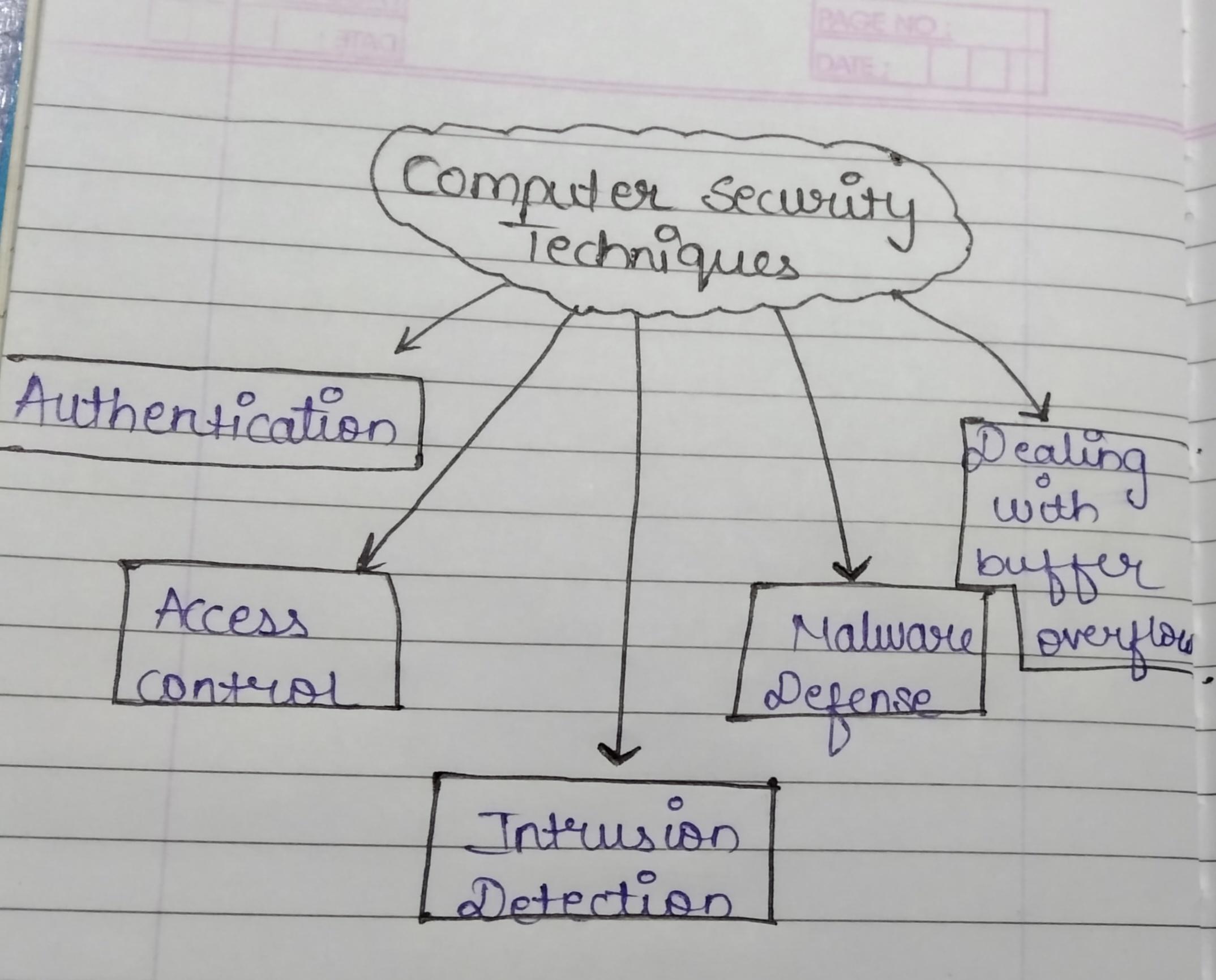
Computer Security Techniques
1. Computer Security, also referred to as cybersecurity, is the practice of protecting computer systems, networks, and data from theft, damage, and unauthorized access.
2. It involves implementing measures that prevent and respond to security threats, ensuring the confidentiality, integrity, and availability of information.
3. Several techniques are used to protect computer systems.
4. Below are explanations of the key techniques like Authentication, Access Control, Intrusion Detection, Malware Defense, and Buffer Overflow Attack mitigation.
•Authentication :
(I) Authentication is the process of verifying a user's identity before granting access to sensitive data or systems. Common forms include password-based, multi-factor, biometric, and token-based. (II) These methods ensure only authorized individuals can access sensitive data and systems, reducing vulnerability to attacks.
•Access control :
(I) Access Control is a system mechanism that restricts access to specific resources. It can be discretionary, mandatory, role-based, or access control lists.
(II) Discretionary Access Control (DAC) determines access and permissions, Mandatory Access Control (MAC) assigns permissions based on security policies, and Role-Based Access Control (RBAC) assigns access based on roles within an organization.
•Intrusion Detection :
(I) Intrusion Detection Systems (IDS) monitor network traffic to detect unauthorized access or activities.
(II) They can be Signature-Based, Anomaly-Based, Host-Based, or Network-Based, focusing on incoming and outgoing traffic, log files, configuration changes, and process behavior.
•Malware Defense :
(I) Malware, including viruses, worms, trojans, and ransomware, infiltrates systems without user knowledge.
(II) Defending against it involves antivirus software, firewalls, sandboxing, and regular updates/patches to prevent malware from affecting systems.
•Dealing with Buffer Overflow Attacks :
(I) Buffer overflow attacks occur when a program writes more data than it can hold, potentially leading to malicious code execution.
(II) Defenses include bounds checking, data execution prevention, address space layout randomization, and safe programming practices like using memory-management languages like Java or Python.