


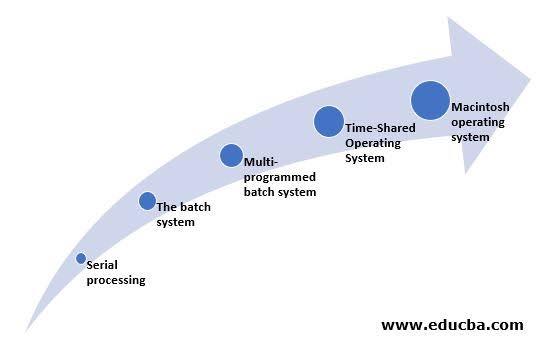
The development of modern operating systems (OS) has been a complex and multi-stage process involving advancements in hardware and software. Here are the key milestones:
1. Early Systems (1950s-1960s)
- Batch Processing Systems: Early computers were programmed with punch cards and tapes. Operating systems like IBM's early batch systems managed job sequencing.
- Time-Sharing Systems: In the 1960s, systems like CTSS (Compatible Time-Sharing System) allowed multiple users to interact with a computer simultaneously, laying the groundwork for multi-user operating systems.
2. Mainframe and Minicomputer Operating Systems (1960s-1970s)
- UNIX: Developed at AT&T's Bell Labs in 1969, UNIX introduced concepts like hierarchical file systems, simple and powerful command-line interfaces, and modular design. It became the foundation for many later systems.
- Multics: An influential but complex OS that contributed many ideas to UNIX and other operating systems.
3. Personal Computer Operating Systems (1970s-1980s)
- MS-DOS: In the early 1980s, Microsoft's MS-DOS became the dominant OS for IBM PCs. It was a simple, command-line-based OS.
- Mac OS: Apple's Macintosh, released in 1984, featured a graphical user interface (GUI), making computers more accessible to the general public.
4. Graphical User Interface and Networking (1980s-1990s)
- Windows: Microsoft introduced Windows in 1985 as a GUI for MS-DOS. Windows 3.0 (1990) and Windows 95 (1995) became widely adopted, combining GUI with improved usability and networking capabilities.
- UNIX and Linux: UNIX systems like Solaris, and later Linux (developed by Linus Torvalds in 1991), offered robust, networked, multi-user capabilities. Linux, being open-source, saw widespread adoption in servers and eventually desktops.
- Networking and Internet: The rise of the internet in the 1990s necessitated better network support in operating systems, leading to the development of protocols and services integrated into the OS.
5. Modern Operating Systems (2000s-present)
- Windows NT and Successors: Microsoft transitioned to the NT kernel with Windows NT (1993), which formed the basis for all future Windows versions (like Windows XP, 7, 10, and 11), combining stability, security, and user-friendly interfaces.
- macOS: Apple's macOS, evolved from Mac OS X (2001), is based on UNIX (specifically NeXTSTEP, a UNIX variant developed by NeXT).
- Linux Distributions: Various Linux distributions (e.g., Ubuntu, Fedora) have become popular for desktops, servers, and embedded systems, known for their security, flexibility, and open-source nature.
- Mobile Operating Systems: The rise of smartphones introduced mobile operating systems like iOS (based on macOS) and Android (based on Linux). These systems are optimized for touch interfaces and mobile hardware.
6. Cloud and Virtualization (2010s-present)
- Cloud Computing: Operating systems adapted to support virtualization and cloud services. Platforms like Amazon Web Services (AWS) and Microsoft Azure provide virtualized instances of operating systems.
- Containers: Technologies like Docker and Kubernetes enable lightweight, portable application deployment, revolutionizing software development and deployment practices.
7. Future Trends
- Artificial Intelligence: Integration of AI and machine learning to enhance performance, security, and user experience.
- Security: Continued focus on security features, including secure boot, encryption, and advanced authentication methods.
- IoT: Operating systems designed for the Internet of Things (IoT), like Google's Fuchsia, aim to provide seamless connectivity and operation across various devices.
The evolution of operating systems reflects advances in hardware, the growing complexity of software applications, and the increasing need for security, usability, and networking capabilities.
Created By:
Krish kaunder
53003230141