


There are two main threading models in process management:
• User-level threads:-
In this model, the operating system does not directly support threads. Instead, threads are managed by a user-level thread library, which is part of the application. The library manages the threads and schedules them on available processors. The advantages of user-level threads include greater flexibility and portability, as the application has more control over thread management. However, the disadvantage is that user-level threads are not as efficient as kernel-level threads, as they rely on the application to manage thread scheduling.
• Kernel-level threads:-
In this model, the operating system directly supports threads as part of the kernel. Each thread is a separate entity that can be scheduled and executed independently by the operating system. The advantages of kernel-level threads include better performance and scalability, as the operating system can schedule threads more efficiently. However, the disadvantage is that kernel-level threads are less flexible and portable than user-level threads, as they are managed by the operating system.
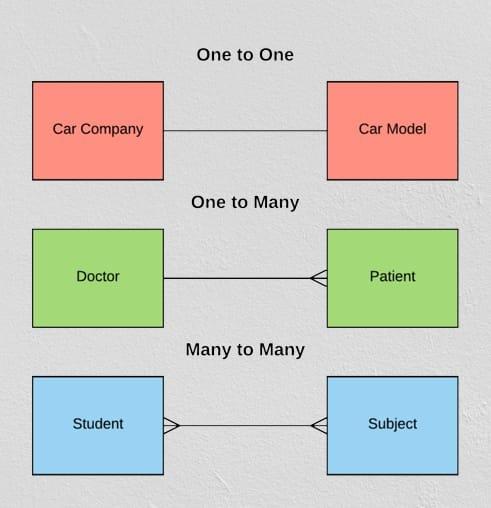
1. Many to Many Model:
In this model, we have multiple user threads multiplex to same or lesser number of kernel level threads. Number of kernel level threads are specific to the machine, advantage of this model is if a user thread is blocked we can schedule others user thread to other kernel thread. Thus, System doesn’t block if a particular thread is blocked. It is the best multi threading model.
2. Many to One Model:
In this model, we have multiple user threads mapped to one kernel thread. In this model when a user thread makes a blocking system call entire process blocks. As we have only one kernel thread and only one user thread can access kernel at a time, so multiple threads are not able access multiprocessor at the same time. The thread management is done on the user level so it is more efficient.
3. One to One Model:
In this model, one to one relationship between kernel and user thread. In this model multiple thread can run on multiple processor. Problem with this model is that creating a user thread requires the corresponding kernel thread. As each user thread is connected to different kernel , if any user thread makes a blocking system call, the other user threads won’t be blocked.