


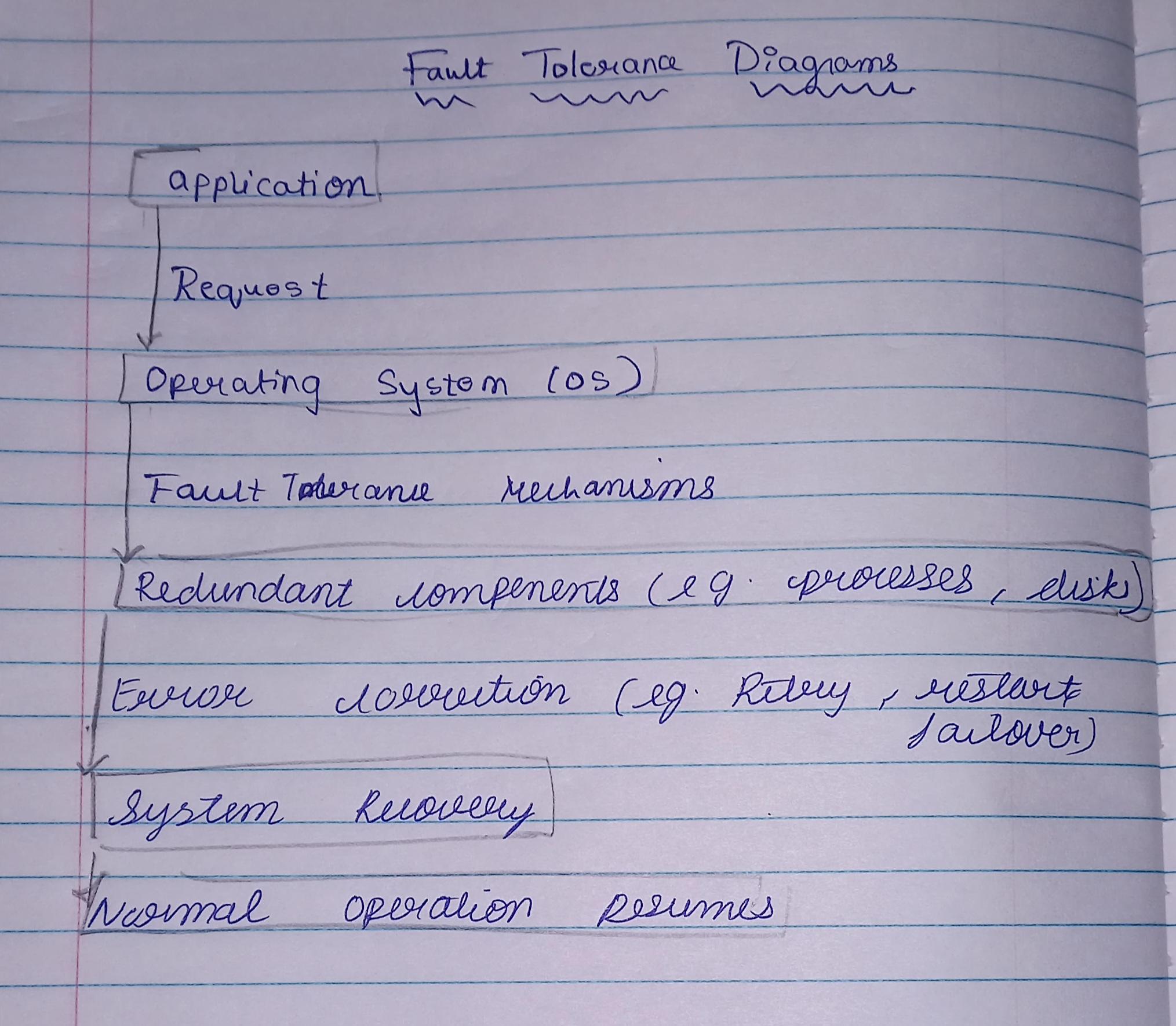
Here's a detailed explanation of fault tolerance, broken down into its key components:
*Fault Tolerance:*
- *Definition:* The ability of a system to continue functioning even when one or more components fail or encounter errors.
*Key Components:*
1. *Redundancy:*
- Duplicate critical components to ensure continued operation.
- Examples: redundant servers, disks, power supplies, network connections.
2. *Error Detection and Diagnosis:*
- Identify and diagnose errors or faults using techniques like:
- Error-correcting codes (ECC)
- Checksums
- Heartbeat mechanisms
- Log analysis
3. *Error Correction:*
- Recover from errors or faults using techniques like:
- Retry
- Restart
- Failover (switch to backup component)
- Rollback (revert to previous state)
4. *Fault Isolation:*
- Isolate faulty components to prevent failure propagation.
- Examples: process isolation, memory protection, device isolation.
5. *Fault Recovery:*
- Restore system functionality after fault correction.
- Examples: process restart, system reboot, failback (return to primary component).
*Techniques:*
1. *Hardware Redundancy:*
- Duplicate hardware components (e.g., disks, power supplies).
2. *Software Redundancy:*
- Duplicate software components (e.g., processes, threads).
3. *Time Redundancy:*
- Use temporal redundancy to repeat tasks or operations.
4. *Information Redundancy:*
- Use data redundancy to detect and correct errors (e.g., ECC, checksums).
*Benefits:*
1. *High Availability:* Minimize system downtime and ensure continuous operation.
2. *Reliability:* Reduce the likelihood of system failures and errors.
3. *Maintainability:* Simplify maintenance and repair processes.
4. *Performance:* Ensure consistent system performance despite faults.
*Challenges:*
1. *Complexity:* Fault-tolerant systems can be complex and difficult to design.
2. *Cost:* Implementing fault tolerance can increase system costs.
3. *Performance Overhead:* Fault-tolerant mechanisms can introduce performance overhead.
By understanding these components, techniques, benefits, and challenges, you can design and implement effective fault-tolerant systems