Name :Vrushti Hindocha SyBSC_IT-B
Sap id-53003230022
Operating system
Topic : Memory Management
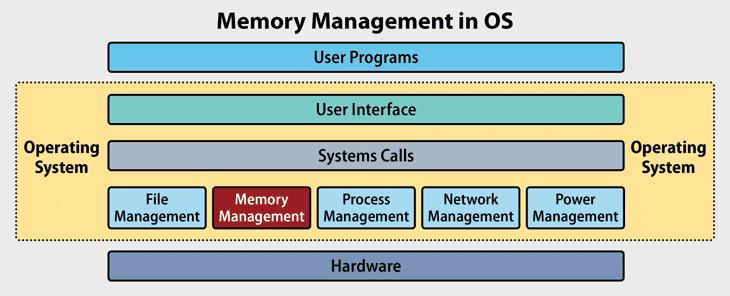
• Memory Management is a vital component of Operating Systems that manages the allocation and deallocation of memory for running programs. It ensures efficient use of memory, prevents memory-related errors, and provides security by preventing programs from accessing unauthorized memory regions.
• The memory management unit (MMU) plays a crucial role in this process, translating virtual addresses used by programs to physical memory addresses. The MMU also enforces memory protection, preventing programs from accessing memory regions outside their allocated space.
• The operating system uses various techniques to manage memory, including:
- Memory Partitioning: Dividing memory into fixed-size partitions for allocation.
- Paging: Dividing memory into fixed-size blocks (pages) for allocation and swapping.
- Segmentation: Dividing memory into logical segments (e.g., code, data, stack) for allocation.
- Virtual Memory: Using a combination of physical memory and secondary storage (e.g., hard disk) to provide more memory than physically available.
• Memory allocation algorithms, such as First-Fit, Best-Fit, and Worst-Fit, are used to allocate memory to programs. Garbage collection is used to automatically reclaim memory occupied by unused programs or data.
• Memory mapping is used to map virtual addresses used by programs to physical memory addresses. Page replacement algorithms, such as Least Recently Used (LRU) and Optimal, are used to replace pages in physical memory with pages from secondary storage when physical memory is full.
• Memory compaction is used to reclaim memory by compacting allocated memory to remove gaps. Memory swapping is used to temporarily transfer pages from physical memory to secondary storage to free up memory.
• Cache memory is used to store frequently accessed data to reduce main memory access. The operating system also provides memory protection features, such as memory segmentation and paging, to prevent programs from accessing unauthorized memory regions.
In addition, modern operating systems use advanced memory management techniques, such as:
- Demand paging: Loading pages into memory only when needed.
- Page coloring: Allocating pages based on their color (size) to reduce fragmentation.
- Memory compression: Compressing memory to reduce usage.
- Memory migration: Migrating processes to different nodes in a distributed system to balance memory usage.
In conclusion, memory management is a critical component of operating systems that ensures efficient, secure, and reliable memory allocation and deallocation for running programs. The operating system uses various techniques and algorithms to manage memory, providing a robust and efficient memory management system.