


Today operating systems are the backbone of our digital world. These software machines power computers, phones, and gadgets, letting them easily use hardware and run apps. They provide user-friendly interfaces, and keeping things safe and steady. It takes complex hardware stuff and makes it simple for apps to use. This makes life easier for everyone.
Modern operating systems also provide numerous services, such as interprocess communication, file and directory systems, data transfer over networks, and a command language for invoking and controlling programs.
Take multitasking - It tasks so fast, you can never imagine your computer's doing a bunch of things at once, act lets you run a bunch of apps side by side.The virtual machine visible to the user is only the outermost of a series of software layers refining the base hardware.
A major function of the operating system is to hide all this complexity and give the programmer a more convenient set of instructions to work with.
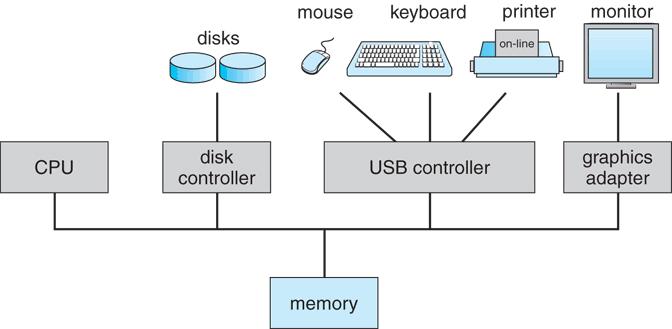
These software modules are best known as device drivers in the most popular personal computer systems and are sometimes treated as parts of the operating system. The interface to the device drivers is usually in a primitive format, called machine language.
The principle behind the layered architecture is called information hidin g confining the details of managing a class of “objects” in a module that has a friendly interface with its users.
Moreover, modern operating systems provide a graphical user interface (GUI) that enables users to interact with their devices through visual elements such as icons, windows, and menus. This GUI simplifies complex operations like file management, application launching, and settings configuration, making computing more accessible to users
Security refers to various security measures to protect against unauthorized access, malware, and data breaches.
OS protects against hackers and viruses, with Passwords, encryption, etc. Your precious data stays locked, whether it's your personal company files.
Operating systems make devices talk to each other and network. More further, a modern operating system is essential for software that enables computers and devises to function effectively and efficiently. As operating systems evolve with it, includes new features and capabilities to meet new growing demands of users.