



Introduction:
E-mail hacking poses a real danger to people and businesses. Hackers use various tricks to break into e-mail accounts, including phishing, trickery, and a technique called SQL injection.
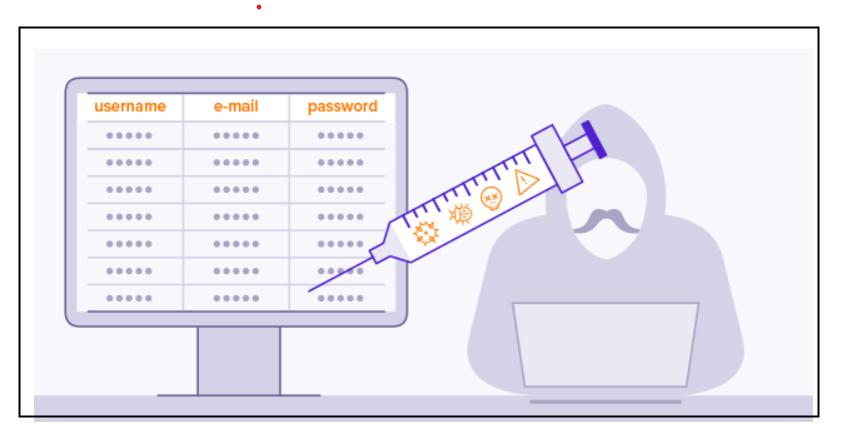
SQL injection is a tricky way hackers mess with web applications. They sneak in harmful SQL code, like a secret code, into an app. This code can then open the app's "safe," giving the hackers access to things they shouldn't see, like passwords and e-mails.
In this blog post, we'll look into whether using SQL injection can help stop e-mail hacking. We'll also talk about good ways to avoid these tricky attacks.
Background:
SQL injection tricks have been around for a while and are still quite effective. A report by the Open Web Application Security Project (OWASP) in 2022 said that SQL injection is the most common way to break into web apps.
There's a reason why these attacks work so well. First, they're pretty easy to do. Hackers just need to slip in that harmful SQL code into a weak app. Second, these attacks are tough to spot. Lots of apps don't properly check what people type in, which leaves them open to these sneaky tricks.
Imagine you have a list of employees in a computer database, and one of the details about each employee is their name. On the front-end side of things, there's a search feature that lets you find employees by their names. Behind the scenes, in the programming part called the "controller," a special kind of code is written to look for the employee's name you're searching for. It might look like this:
$query = "SELECT * FROM employee WHERE emp_name = '$emname' ";
Now, here comes the tricky part. Let's say there's a person who wants to do something bad, like get access to all the employee data even if they shouldn't. This person goes to the search feature and instead of typing in a real employee's name, they type in a special code:
OR '1' = '1'
What happens next is important. The search code changes to something like this:
$query = "SELECT * FROM employee WHERE emp_name = '' OR '1' = '1' ";
The part that says '1' = '1' is always true. So, when this happens, the code thinks, "Okay, show me all the employee data," and it gives the attacker access to all the information about all the employees, which they're not supposed to have.
This is like tricking the computer program by giving it some special words that make it do things it shouldn't. It's a way that hackers can use to get into systems and see things they're not supposed to see.
People have done studies to see if using SQL injection can help stop e-mail hacking. Overall, these studies say it can help, but it's not perfect.
One study, done by the University of Maryland, found that using SQL injection stopped 80% of e-mail hacking tries. But, it didn't work against all types of hacking. For example, it didn't stop tricks that aimed at your web browser.
Another study by the National Institute of Standards and Technology (NIST) found that SQL injection blocked 60% of e-mail hacking attempts. It worked better against attacks on the app's database.
There are a number of best practices that can be used to prevent SQL injection attacks. These include:
Conclusion:
SQL injection is a serious security threat, but it can be prevented by following the best practices outlined above. By taking steps to prevent SQL injection attacks, organizations can help to protect their e-mail systems from hackers.