



In an increasingly interconnected world, network security has become paramount. While cyberattacks take on various forms, one that often flies under the radar but poses a significant threat is the jamming attack. Jamming attacks target the communication infrastructure of networks, disrupting the flow of data and causing chaos. In this article, we will explore the ins and outs of jamming attacks in network security, their methods, consequences, and ways to mitigate them.
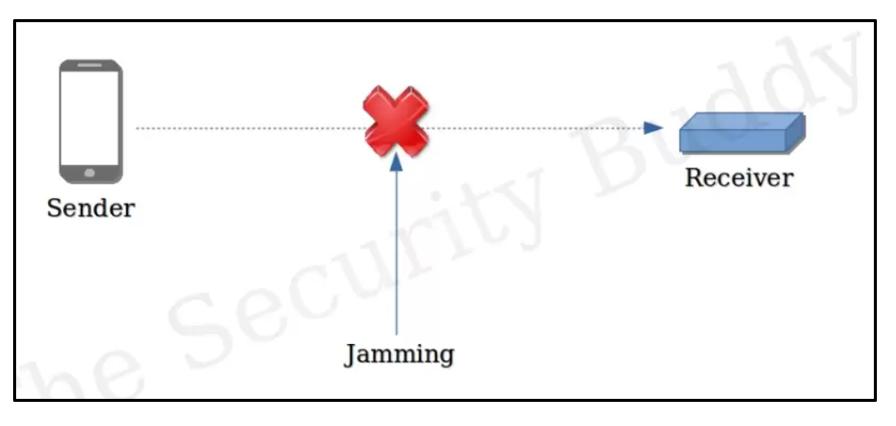
A jamming attack is a type of malicious activity in the field of network security and communication systems. It involves the intentional interference or disruption of wireless communication signals using various techniques and devices. The primary goal of a jamming attack is to disrupt or disable the normal functioning of wireless communication systems, such as Wi-Fi networks, cellular networks, radio frequency identification (RFID) systems, and more. This interference typically takes place in the radio frequency (RF) spectrum used by these communication systems.
If successful, an attacker who takes these steps can block the network on a small or large scale, depending on the severity of the intended attack. An important way to mitigate potential fraud attempts tailored to jamming attacks is to protect yourself with various fraud detection techniques and fraud prevention software.
Methods of Jamming Attacks
Continuous Wave (CW) Jamming: In this method, a jammer emits a continuous signal on the target frequency, effectively drowning out legitimate signals. This approach is relatively straightforward and easy to implement but lacks sophistication.
Reactive Jamming: Reactive jammers monitor the target communication channel and activate jamming when they detect legitimate signals. This method makes it harder for network defenders to detect and counteract the jamming attack.
Deceptive Jamming: Deceptive jammers attempt to mimic legitimate signals, making it challenging for the target system to differentiate between genuine and malicious signals. This method requires a deep understanding of the target communication protocol.
Disruption of Services: Jamming attacks can lead to a complete disruption of wireless communication services. This can have severe consequences in critical infrastructure systems such as transportation, healthcare, and emergency services.
Financial Losses: Businesses relying on wireless networks for their operations can suffer significant financial losses due to downtime caused by jamming attacks. Loss of revenue, productivity, and customer trust are common outcomes.
Security Risks: Jamming attacks can be used as a diversion tactic to distract security personnel while other malicious activities take place. This poses a significant security risk, as critical security systems may be compromised during the attack.
Public Safety Concerns: Jamming attacks in critical situations, such as during a disaster or emergency, can jeopardize public safety by disrupting communication between first responders and emergency services.
Frequency Hopping: Utilizing frequency hopping spread spectrum (FHSS) or dynamic channel selection can make it harder for jammers to disrupt communication. These techniques involve switching between different frequencies rapidly, making it challenging for jammers to keep up.
Encryption: Employing strong encryption protocols can protect the integrity and confidentiality of data transmitted over wireless networks, even if the jammer succeeds in disrupting the signal.
Signal Strength Monitoring: Continuous monitoring of signal strength and quality can help detect jamming attacks. Anomalies in signal strength can trigger alerts, allowing for a rapid response to mitigate the attack.
Jammer Detection Systems: Deploying specialized jammer detection systems can identify and locate jamming sources, enabling authorities to take appropriate action.
Redundancy and Backup Systems: Implementing backup communication systems and redundancy can ensure that critical services remain operational even in the face of a jamming attack.
Jamming attacks can take various forms and can target a wide range of wireless communication systems. Here are some examples of jamming attacks in different contexts:
Wi-Fi Jamming: In this scenario, an attacker uses a jamming device to disrupt Wi-Fi networks in public places, such as coffee shops, airports, or hotels. By flooding the airwaves with interference signals, the attacker can disrupt the Wi-Fi service, preventing legitimate users from connecting to the network.
Cellular Network Jamming: Attackers may deploy jamming devices in areas where they want to disrupt cellular communication. For instance, in a prison setting, inmates have been known to use improvised jamming devices to prevent inmates from using mobile phones within the facility.
GPS Jamming: Jamming attacks can target Global Positioning System (GPS) signals. For example, a jamming device placed in a vehicle could interfere with the GPS reception, causing navigation systems to malfunction and potentially leading to incorrect routes or location information.
Radio and Television Broadcasting Jamming: In some cases, jamming attacks are aimed at radio and television broadcasts. These attacks can disrupt broadcasts by transmitting interference signals on the same frequencies as the targeted stations, leading to audio or video disruptions.
Jamming attacks pose a significant threat to network security, potentially leading to service disruption, financial losses, and security risks. As technology continues to advance, so do the methods and capabilities of jammers. Network security professionals must remain vigilant and adopt proactive measures to detect, prevent, and mitigate the impact of jamming attacks. By employing robust encryption, frequency hopping, and monitoring systems, we can better protect our wireless communication networks from the disruptive effects of jamming attacks, ensuring the reliability and security of our interconnected world.