Hello Thunders!
Proof of work is one of the most important aspects of the virtual world, especially virtual trading world or exchanges including blockchains. Whether it is bitcoin blockchain, ethereum or the steem, every blockchain exhibits certain algorithms called as Proof of Work or PoW. PoW is another concept that is taken from daily human life. If you see blockchain closely then you will find that all the blockchain system lies in its simplicity and close-less-ness to the real world. The "Real World" is the similar concept that you have heard while your programming lectures. Object-Oriented Programming? Mapping real-world entities by using or defining them as objects and binding them around there methods! PoW is the innovation and an invention of blockchain technology, which is now the most important thing that a blockchain system has. PoW has numerous definition based on their use and application in a system. Steemit has its own version of PoW called as DPoS(Delegated Proof of Stake) whereas Ethereum is based on a hybrid version of PoS(Proof of Stake).

Image source:- bitcoinwiki.org
Back to old days!
- Proof of Work isn't something which is recently created or adopted, it was there when we were in school. Believe me! okay, blockchain system is one of the fundamental foundations of upcoming technologies and one of the main reason behind this is that blockchain is close to what we humans think and do. In every aspect, you will find that blockchain is pretty relatable to human society.
- Back in school days, we used to get a lot of writing homework to memorize certain concepts or meanings. And we simply hate that from the deep of the heart, sigh! Sometimes we do not use to carry that homework to our teacher or make an excuse in case of incomplete homework or assignment. Let's take a case here, what if I do not write the homework and just memorize it? I can do it! But what if my teacher asks me to show the work? yes, I have learned it orally but what is the proof? The proof is my homework notebook where I have written the things that I was told by the teacher.
- Let's take another example, Assume that you have bought a plot and some government bodies came for an inquiry. How will you justify that this particular plot belongs to me or it is my property? Paper Works! All the official papers that were signed while buying a plot is now the proof that will justify that this plot is yours. In this case, all that official papers are the proof of work!
- So for every task or work which we complete, we generate a PoW in some manner. But the generated PoW must be in a format that clears all the protocols that are required for an authentic PoW.
Blockchain PoW
Image source:- realdolmen.com
- The blockchain is in the mainstream which is maximizing the capabilities of PoW. To understand it more clearly we will take a quick look on Bitcoin blockchain for the same.
- Miners are the backbone of Bitcoin blockchain which is also responsible for validating a block. The blockchain is a term made of two independent words - Block and Chain. Independent word? Yes, Block is a unit of a given size which consists of certain things. In term of bitcoin, a block can have 'n' number of transactions happened in a given time period. These blocks are arranged in a sequential chain order where each block has some hash function which is used to interconnect and validate them. (n is having hash for n+1 block whereas n is also having a hash function for n-1. This reads like "n-1 -- n -- n+1" where each successor block validates the upcoming block)
- Miners used to generate these blocks or simply mine this blocks. Mining requires a lot of calculation and solution for complex mathematical expressions. In starting phase all the miners are competing with each other to find a solution. When a miner tops the table by finding the solution in the least time other defeated miners use to validate the solution obtained by the topper. Calculation, solution, verification, and validation are PoW here. After validation, the mined block is chained in the series and the topper will now get some fixed amount of bitcoins in rewards!
- This is how PoW works in bitcoin blockchain. These concepts are similar(not same) in every crypto blockchain. There are various hybrid models of PoW and these hybrid models are the custom models made for the particular application and operation.
How PoW is helping!
- Apart from validating or justifying a work, PoW is also playing a vital role to stop spam and abusers. Cheaters are always waiting for a chance to break-out in the system and cause trouble in the process. The only aim of abusers is to make a lot out from a breakage.
- So how it is helping? Let's take one more example here, many the times you help out your friend by sharing or sometimes handing over all your homework and your friend just copies your works. And many the times' teachers caught this copy-cases. Based on your pattern, word selection, writings, previous works they find out that it is a copy case or an authentic/original work. Now if the teacher finds the same(copied) work or denying the instructions while completing a work, he/she cancels the work. The similar thing happens in PoW.
- PoW helps to identify an authentic work, and authentic/validated work makes a blockchain system. While validation some more work is required which constitutes to overall PoW. In bitcoin blockchain, every transaction is accompanied with some mathematical expressions which are needed to be solved and then sent back for validation/verification. So this is how a valid transaction is submitted and PoW is obtained! I hope that you now know the basics of PoW and how it is becoming a prominent part of the blockchain system.
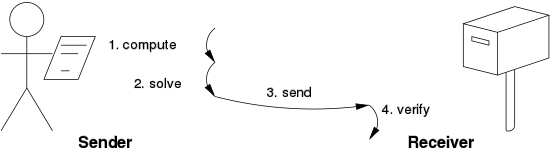
Image source:- wikipedia.com
That's all for Now!
Timeets | Wisemonkeys