


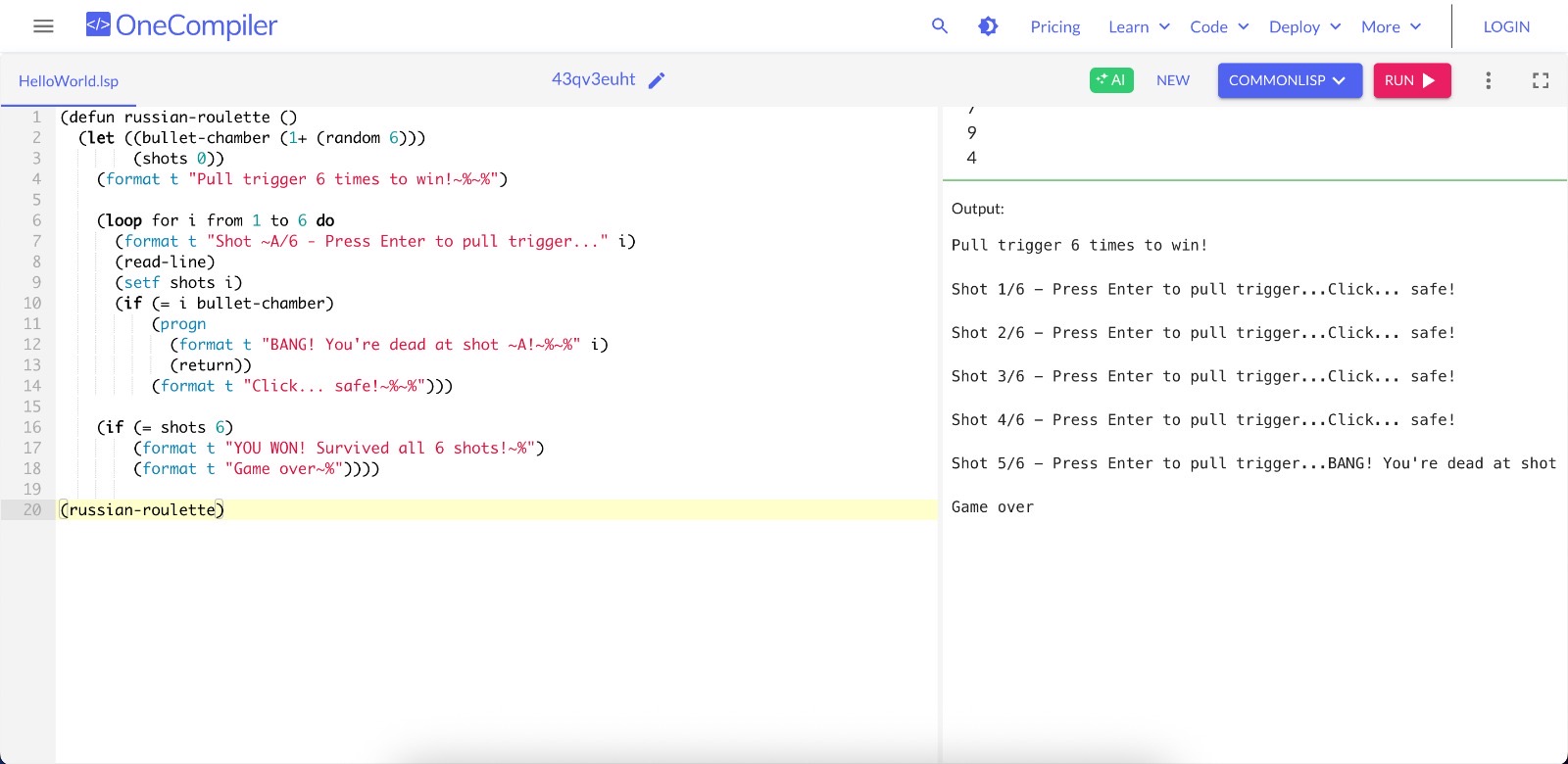
(defun russian-roulette ()
(let ((bullet-chamber (1+ (random 6)))
(shots 0))
(format t "Pull trigger 6 times to win!~%~%")
(loop for i from 1 to 6 do
(format t "Shot ~A/6 - Press Enter to pull trigger..." i)
(read-line)
(setf shots i)
(if (= i bullet-chamber)
(progn
(format t "BANG! You're dead at shot ~A!~%~%" i)
(return))
(format t "Click... safe!~%~%")))
(if (= shots 6)
(format t "YOU WON! Survived all 6 shots!~%")
(format t "Game over~%"))))
(russian-roulette)