


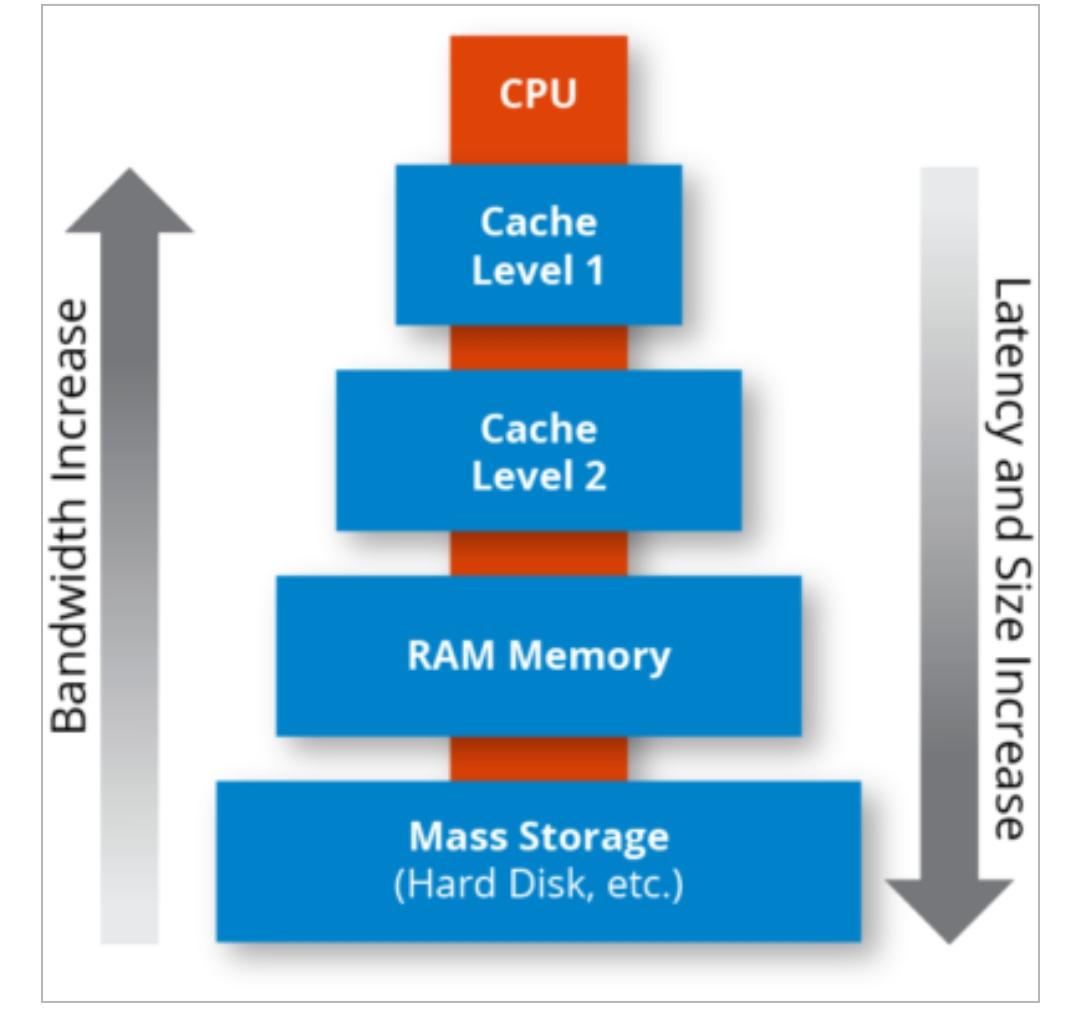
Cache memory is a type of computer memory that is used to store frequently accessed data for quick retrieval. It is located on the CPU chip itself and is much faster than main memory (RAM).
Cache memory is organized into levels. Level 1 (L1) cache is the smallest but fastest, located directly on the CPU chip. It is used to store instructions and data that are frequently accessed by the CPU. Level 2 (L2) cache is larger but slower, and is typically located on the motherboard. Level 3 (L3) cache is even larger but slower, and is often shared between multiple CPU cores.
The purpose of cache memory is to improve the overall performance of the computer by reducing the number of times the CPU has to access main memory.